This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
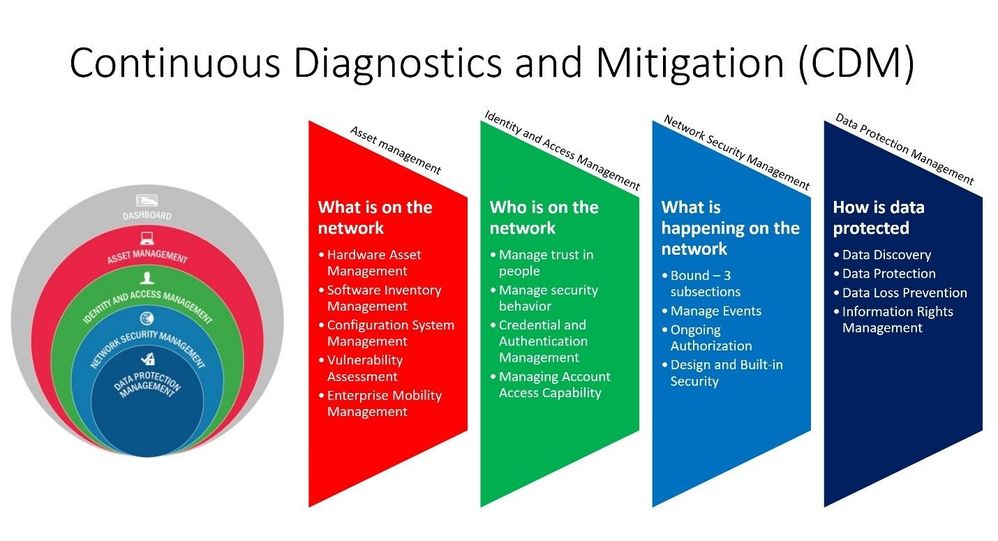
In August of 2012, the Continuous Diagnostics and Mitigation (CDM) program was formed to help federal agencies improve cyber security and provide visibility across the federal government. The program has been expanded recently with the following OMB memo adding Endpoint Detection and Response (EDR).
CMD is made up of 4 capabilities areas:
- Asset management |What is on the network?
- Identity and Access Management | Who is on the network?
- Network Security Management | What is happening on the network?
- Data Protection Management | How data is protected?
Figure 1: CDM Overview
The first set of capabilities, Asset Management has five main subordinate capabilities.
- Hardware Asset Management (HWAM)
- Software Inventory Management (SWAM)
- Vulnerability Management (VUL).
- Configuration System Management (CSM)
- Enterprise Mobility Management (EMM)
This blog series will focus on Asset Management - What is on the network and will be released in four parts. This post will focus on Hardware Asset Management (HWAM); more information about the CDM program and HWAM can be found here HWAM.
Microsoft 365 Defender
Microsoft 365 Defender is a unified pre- and post-breach enterprise defense suite that natively coordinates detection, prevention, investigation, and response across endpoints, identities, email, and applications to provide integrated protection against sophisticated attacks.
With the integrated Microsoft 365 Defender solution, security professionals can stitch together the threat signals that each of these products receive and determine the full scope and impact of the threat; how it entered the environment, what it's affected, and how it's currently impacting the organization. Microsoft 365 Defender takes automatic action to prevent or stop the attack and self-heal affected mailboxes, endpoints, and user identities.
The following solutions are a part of Microsoft 365 Defender, for more information about each solution select the link below:
- Defender for Office
- Defender for Endpoint
- Defender for Cloud
- Defender for Identity
- Defender for Cloud Apps
This blog will focus on the Microsoft Defender for Endpoint solution only and how it related to CDM.
Microsoft Defender for Endpoint
Since 2012 many new tools have emerged, and frameworks like Zero Trust have changed the market. Microsoft Defender for Endpoint (MDE) can help organization improve their security posture, improve operational efficiency, and meet several CDM mandates. MDE is an Endpoint Protection Platform (EPP) and Endpoint Detection and Response (EDR) solution located in the leader’s quadrant of the Gartner MQ . MDE is a solution in the Microsoft Extended Detection Response (XDR) portfolio that is a leader in the new Forrester XDR wave.
Microsoft Defender for Endpoint is an enterprise endpoint security platform designed to help enterprise networks prevent, detect, investigate, and respond to advanced threats. MDE provides several out of the box capabilities to assist organizations with discovering risk and system exposure. The core capabilities of MDE are:
- Endpoint Behavioral Sensors
- Cloud Security Analytics
- Threat Intelligence
- Thread and Vulnerability Management
- Attack Surface Reduction
- Next Generation Protection
- Endpoint Detection and Response (EDR)
- Automated Investigations and remediation
- Microsoft Secure Score for Devices
- Microsoft Threat Experts
MDE has several features that will not be outlined in this blog since the focus is on CDM HWAM. For more information on MDE you can use the following link Microsoft Defender for Endpoint | Microsoft Docs
Hardware Asset Management (HWAM)
HWAM is about discovering IP addressable assets on an organizations network to help agencies establish and maintain an authorized hardware inventory baseline and understand their potential risk to exposure. This helps agencies meet data currency requirements to locate the hardware, secure the enterprise and assess the risk to the organization. MDE provides two out of the box experiences to assist with network discovery; network assessment and device discovery.
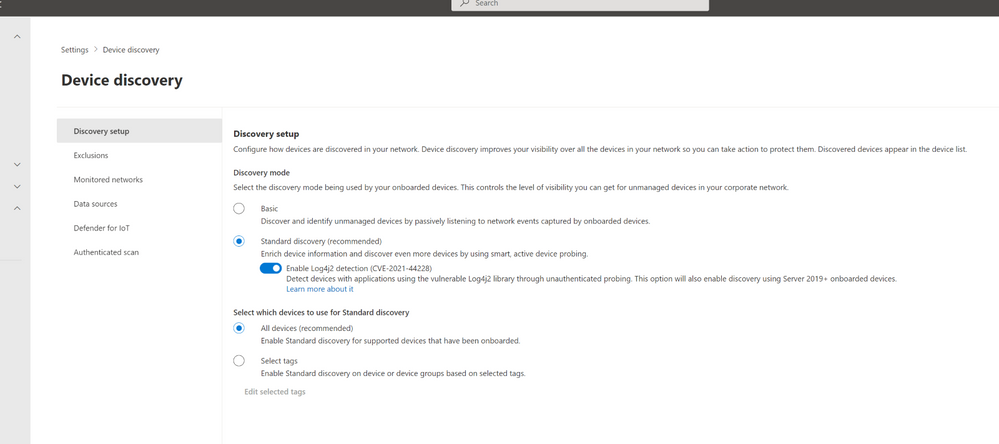
Device Discovery
The first aspect focuses on finding unmanaged (computers and mobile devices) Windows, Linux, Mac, IOS and Android devices on the network. Device discovery turns a MDE managed Windows endpoint into a discovery engine that will use various methods to identify devices connected to your organizations network. Once the service is enabled, with a few quick setup steps an organization can define which devices they would like to use as a discover node and choose between two discovery methods, standard or basic.
Figure 2: MDE Device Discovery Settings
More information about how this feature works can be found here Device discovery overview | Microsoft Docs
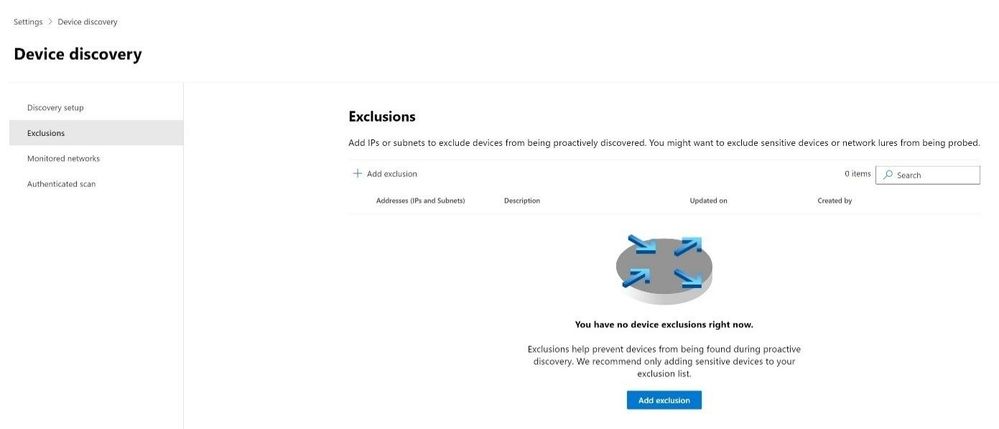
Organizations can exclude a network from discovery by adding IP ranges to an exclusion list. This should be done with caution, so organizations don’t create blind spots on the network.
Figure 3: MDE Network Exclusions
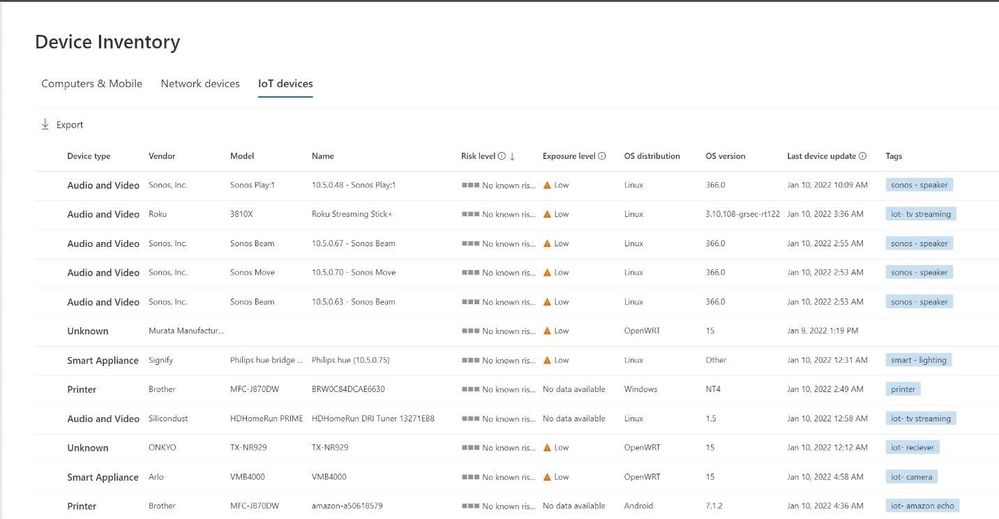
After configuring discovery, MDE will display unmanaged devices in the portal with an onboarding status of “can be onboarded” or “onboarded”.
Figure 4: Example of discovered device
The second feature of discovery will identify other devices connected to network like Televisions, IoT devices, etc. MDE will scan for vulnerabilities on the connected devices to identify outdated firmware and threats as well.
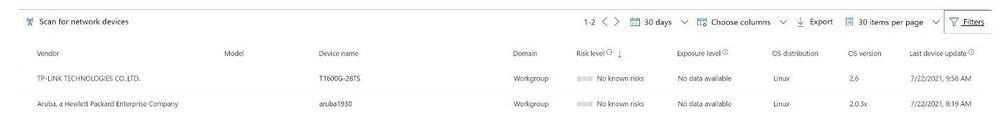
Figure 5 IOT Inventory
MDE can work in conjunction with Microsoft Defender for IoT connecting the two platforms to help discover devices and provide a unified experience for organizations by populating all the discovered assets into the Microsoft security portal.
More information can be found here on the integration How Microsoft Defender for IoT can secure your IoT devices - Microsoft Security Blog
Figure 6 Azure Defender for IoT integration
MDE has third party integrations with solutions like Corelight to enrich information and help provide a unified discovery experience. For more information on this integration can be found here Enable Corelight integration in Microsoft Defender for Endpoint | Microsoft Docs.
Figure 7 Corelight Integration
Network Assessment
Network assessment is focused on devices that are typically managed and agentless like a switch or firewall. MDE can be configured to use SNMP V1 – V3 to connect to network devices and perform a threat assessment of those devices.
Staff will define an Ip address or Ip range to scan and configure the SNMP authentication methods used to connect to the network device(s).
Figure 8 MDE Network Assessment Configuration
Once the assessment has been configured each network device will be displayed in the device inventory section of the MDE interface. MDE will perform a threat assessment for those devices helping organization discover vulnerabilities of the network gear.
Advanced Hunting and API
MDE provides several methods to access data. This can be done graphically in the interface, using the KQL query language, or via an API.
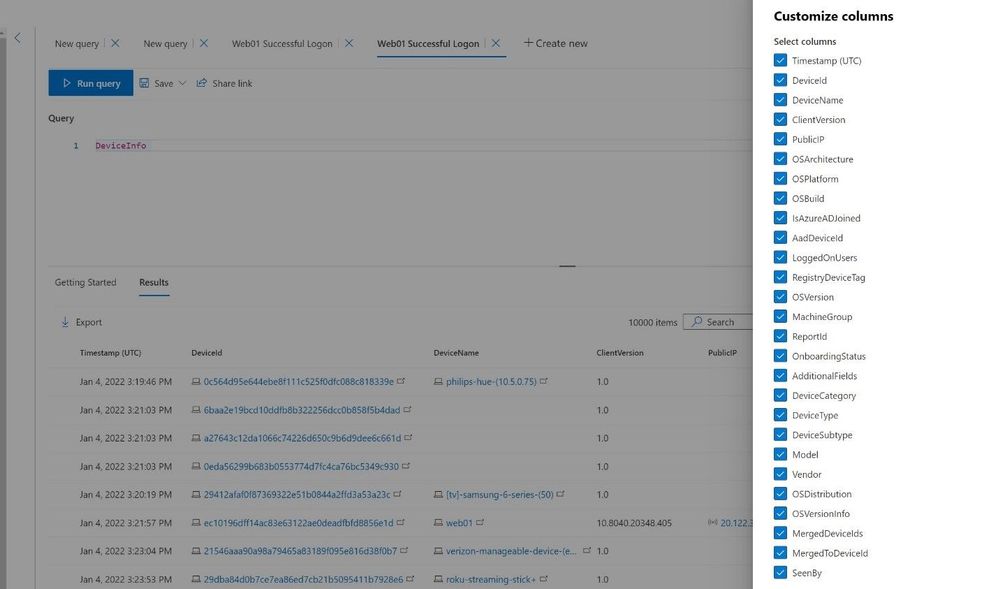
MDE stores the raw data in Advanced Hunting tables based on Kusto Query Language (KQL). The DeviceInfo table will provide staff with a list of all devices that are discovered on the network and provide several pieces of information that can be filtered on like onboarding status, Device Name, Device Seen by, etc.
Figure 10 KQL Device Inventory
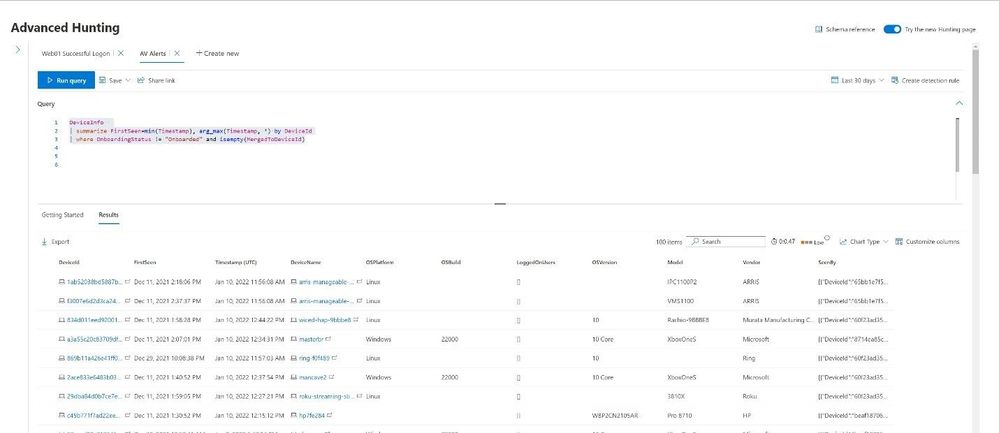
Staff can run a query like the below to pull information on when a device was first seen in the organization and by which device(s).
DeviceInfo
| where Timestamp > ago(30d)
| summarize FirstSeen=min(Timestamp), arg_max(Timestamp, *) by DeviceId
| where OnboardingStatus != "Onboarded" and isempty(MergedToDeviceId)
| where FirstSeen >= ago(1d)
Figure 11 KQL query
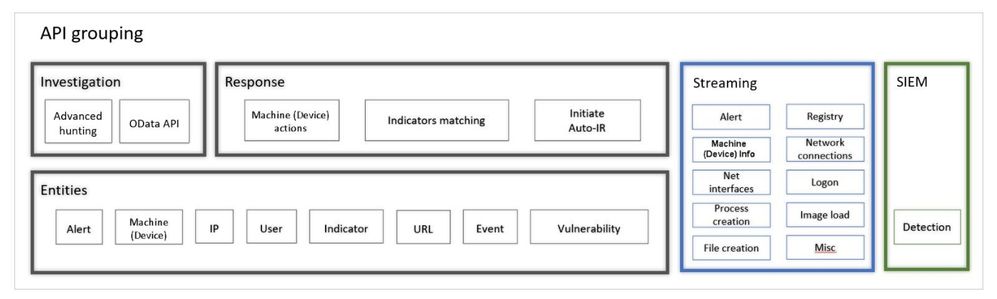
The Defender for Endpoint APIs can be grouped into three categories:
- Microsoft Defender for Endpoint APIs (Entities)
- Response API
- Investigation API
- Raw data streaming API
- SIEM integration
Figure 12: MDE APIs
Using the various API methods organization can access the raw data or a subset of the data hosted in MDE. This helps organization automate tasks, perform selective tasks, and filter data that can be used with other efforts.
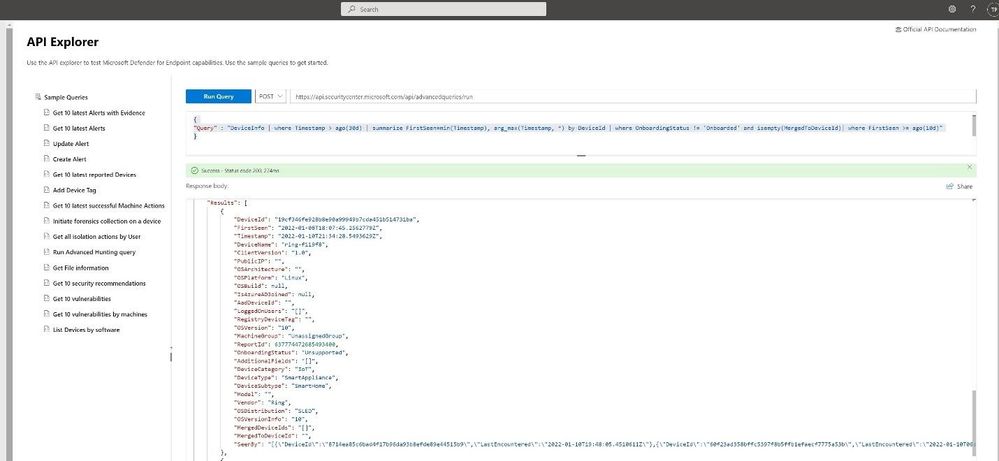
Using the built in API explorer helps staff quickly test syntax and validate the API calls. Once the syntax has been validated staff can use the APIs to push and pull data from the platform or integrate with other tools like SOAR application(s) to automate tasks, pull data into SIEM, or automate incident and response actions.
Using the same KQL query from earlier we can call the hunting API to return the same data set to list any device that has been discovered in the last day.
Post https://api.securitycenter.microsoft.com/api/advancedqueries/run
{
"Query" : "DeviceInfo | where Timestamp > ago(30d) | summarize FirstSeen=min(Timestamp), arg_max(Timestamp, *) by DeviceId | where OnboardingStatus != 'Onboarded' and isempty(MergedToDeviceId)| where FirstSeen >= ago(10d)"
}
Figure 13 API Explorer