This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Community Hub.
Author: Eliran Azulai, Principal Program Manager, Azure Networking
Co-author: Gunjan Jain, Principal PM Manager, Azure Networking
Similar to the Spring4Shell and Log4Shell vulnerabilities, a new critical vulnerability CVE-2022-42889 aka Text4Shell was discovered on October 13, 2022.
Text4Shell is a vulnerability in the Java library Apache Commons Text. This vulnerability, in specific conditions, allows an attacker to execute arbitrary code on the victim's machine (Remote Code Execution or "RCE").
Customers can detect and protect their resources against Text4Shell vulnerability using Azure native network security services, Azure Firewall Premium and Azure Web Application Firewall (WAF). You can utilize one of these services or both for multi-layered defense.
Customers using Azure Firewall Premium, and Azure WAF have enhanced protection for this RCE vulnerability from the get-go. Customers can protect their assets by upgrading their Apache Commons Text version to the patched version 1.10. However, there are situations when upgrading software is not an option or may take a long period of time. In such case, they can use products like Azure Firewall Premium and Azure WAF for protection.
Azure Firewall Premium Configuration
Azure Firewall premium IDPS (Intrusion Detection and Prevention System) ruleset was updated within a few hours to include CVE-2022-42889 vulnerability. Azure Firewall Premium IDPS provides prevention and detection against active network attacks such as this, in a timely manner. Azure Firewall Premium with TLS inspection and IDPS capabilities protects customers against this vulnerability, you should have both TLSi and IDPS capabilities enabled.
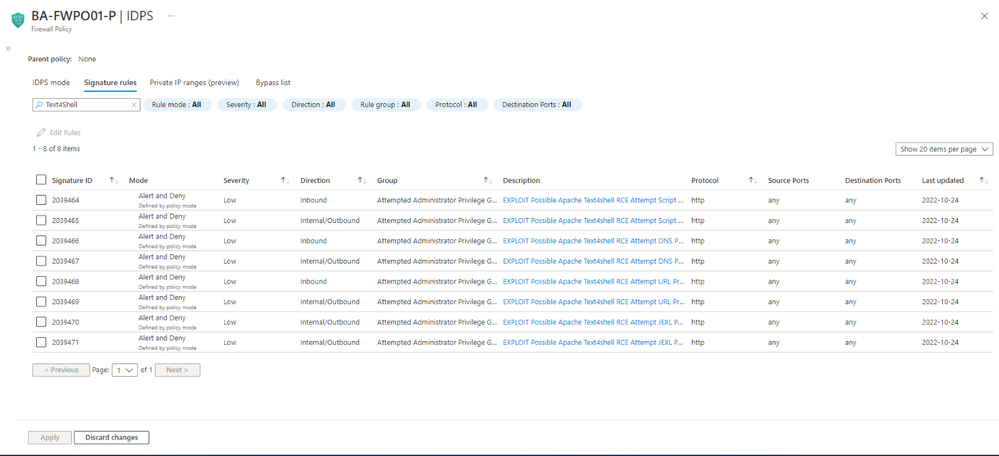
IDPS should be configured either as ‘Alert’ or ‘Alert and Deny’ mode. IDPS signatures assigned with Text4Shell should be visible in Azure Portal in your Azure Firewall Policy as seen below:
Azure Web Application Firewall (WAF) Configuration
Azure WAF includes Microsoft managed rules out of box that provide protection against CVE-2022-42889 vulnerability. These rules are available with all versions of Default Rule Set (DRS) with Azure Front Door global deployments, and with all versions of Core Rule Set (CRS) with Azure Application Gateway regional deployments. There are multiple rules across Java, RCE, and XSS rule groups that help mitigate attack patterns for this CVE. In our internal testing, we found rules 932130 and 941210 to be quite effective in providing protection against this vulnerability. These protection rules are enabled by default to block exploit attempts to this vulnerability.
More information about Default Rule Set (DRS) on Azure WAF with Azure Front Door can be found here. More information about Core Rule Set (CRS) on Azure WAF with Application Gateway can be found here.
Conclusion
At Microsoft, we are continuously monitoring for new & emerging threats to protect customer workloads running in Azure. Our signature pipelines are quickly updated within a few hours of detecting a threat. Customers are recommended to deploy Azure Firewall Premium for outbound network traffic and WAF for inbound HTTP/HTTPs traffic.
We will continue to monitor threat patterns and modify the rules and signatures in response to emerging attack patterns as required.
Learn More
Azure Firewall Premium and Azure WAF provide advanced threat protection capabilities to help detect and protect against Text4Shell and other exploits. For more information on everything we covered above, please see the following documentation: