This post has been republished via RSS; it originally appeared at: Core Infrastructure and Security Blog articles.
Introduction
Hello everyone, Andrew Coughlin here and I am a Cloud Solutions Architect at Microsoft focusing on Azure IaaS. I frequently get asked questions about how to set up private endpoints from my customers that have presence in multi regions. In this blog I will talk about how to set up DNS resolution for a multi-site with a blob container within a storage account with private endpoints.
Environment Setup
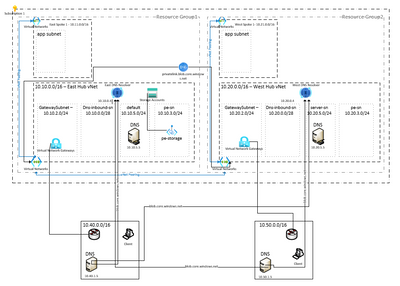
In this discussion I want to first outline what the environment will look like as we talk through this, each customer scenario might be slightly different, but this can be used as a starting point. Most customers will have some form of private connectivity to Azure (Site-to-Site / ExpressRoute). We have a subscription that is tied to an Azure AD tenant with the following resources:
- Virtual Network x 2 (In different regions)
- Virtual Network – Spoke x 2 (In different regions)
- Virtual networks peered via vNet peering
- Site-to-Site VPN connection configured between on premises and Azure
- Storage Account configured with private endpoint
- Private DNS zone for privatelink.blob.core.windows.net in one region
Prerequisites
- Quickstart: Create a virtual network - Azure portal - Azure Virtual Network | Microsoft Docs
- Tutorial: Connect virtual networks with VNet peering - Azure portal | Microsoft Docs
- Azure networking services overview | Microsoft Docs
- Tutorial: Connect to a storage account using an Azure Private Endpoint - Azure Private Link | Microsoft Learn
- Quickstart - Create an Azure private DNS zone using the Azure portal | Microsoft Learn (privatelink.blob.core.windows.net)
Reference Articles
- Azure Private Endpoint DNS configuration | Microsoft Docs
- What is Azure DNS Private Resolver? | Microsoft Docs
Storage account Setup
For a detailed step-by-step instruction on how to create a private link/endpoint for Azure Key vault please see Tutorial: Connect to a storage account using an Azure Private Endpoint - Azure Private Link | Microsoft Learn. However, it is important to point out that on step 6 of Tutorial: Connect to a storage account using an Azure Private Endpoint - Azure Private Link | Microsoft Learn to select the resource group you created the private dns zone for privatelink.blob.core.windows.net. Since this has already been created, we only need 1 private link zone for privatelink.blob.core.windows.net within our subscription.
Once you have completed this step you should have an A record for your storage account in privatelink.blob.core.windows.net:
Azure Private DNS Zone Configuration
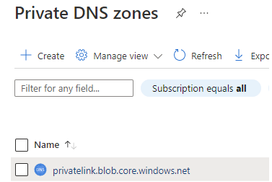
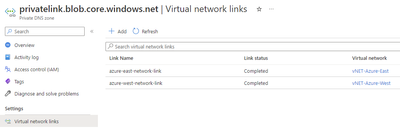
Now that we have the private dns zone configured, we need to link this zone to both of our hub virtual networks. You should only have one privatelink.blob.core.windows.net as having duplicate zones will provide inconsistent responses. You are not able to link the same named private dns zone to the same virtual network, you can however have multiple private dns zones (privatelink.blob.core.windows.net and privatelink.file.core.windows.net) linked to the same virtual network.
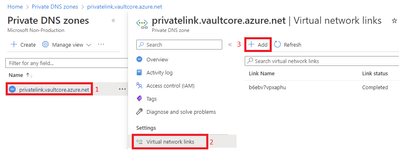
- To do this search for the private dns zone and select privatelink.blob.core.windows.net.
- Click on Virtual Network Links.
- Click Add.
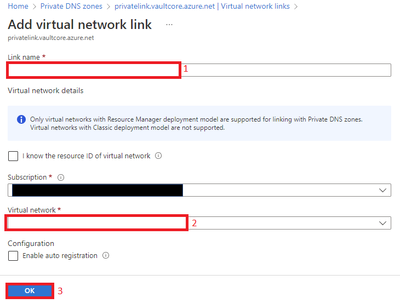
- Type the link name and select the virtual networks and click OK.
- When completed you should have a link for both East vNet Hub and West vNet Hub.
Azure Private DNS Resolver Setup
We currently have DNS resolution working within Azure to resolve to the private ip address of the storage account. But we still are resolving the private ip for our on-premises network. In order to do this, we need to deploy a DNS configuration that meets our needs. Most customers would setup servers to be a DNS forwarder within Azure, however in this example we are going to go with a new generally available feature called Azure DNS Private Resolver. For steps on how to set this up please see Quickstart - Create an Azure private DNS resolver using the Azure portal | Microsoft Docs. Before we setup Azure Private DNS resolver, we first need to make sure we have the following subnets created:
Each Region should have:
- 1 – inbound subnet, minimum: /28, maximum: /24, for each inbound endpoint we want to create.
We will create a Private DNS Resolver in the East vNet Hub and West vNet Hub both with an inbound, outbound endpoint.
Setup Conditional Forwarders from on premises to Azure
Next, we will want to set up conditional forwarders from our on-premises DNS servers to forward all blob.core.windows.net to the east and west inbound ip addresses. You will want to do this for both East on premises and West on premises DNS servers. Some customers may want to change the order to prefer east to forward to east inbound ip address first then west inbound ip address then West on premises to forwarder to west inbound ip address then east inbound ip address.
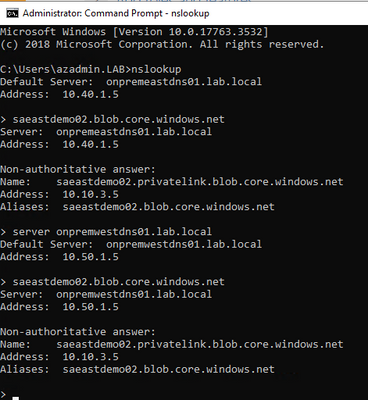
Testing on-premises resolution
The last step is to evaluate our configuration using a machine within the on-premises network. I’m going to validate that saeastdemo02.blob.core.windows.net will now resolve to its private ip addresses both from on-premises east and on-premises west locations:
Conclusion
That’s it, we set up a storage account to be resolvable in a hybrid environment for two on-premises locations connected to Azure in separate regions. If you wanted to set up a storage account in the east and west this could be done the same way, when creating the private endpoint in the west, make sure to use the existing private dns zone that was already created and not create a new private dns zone. If you were using another service, say key vault or another PaaS service that supports private endpoint you would set this up the same way except for the private dns zone names would be different. Thank you for taking the time to read this blog, I hope this helps you and see you next time.