This post has been republished via RSS; it originally appeared at: Microsoft Tech Community - Latest Blogs - .
Recently, a new feature called “Manual effect” popped out to users, but it is still in the PREVIEW stage. It allows users to self-attest the compliance of resources or scopes. In another word, it gives users a chance to determine the evaluation result of the specific resource and the reason. Currently, it is mostly used inside the Security related built-in policies and initiatives. You may check more details from the following doc.
Understand how effects work - Azure Policy | Microsoft Learn
There are multiple built-in policies under the Security category to check the subscription level compliance results with manual effect. For the built-in example, you may check “Issue public key certificates” (policy definition ID: /providers/Microsoft.Authorization/policyDefinitions/97d91b33-7050-237b-3e23-a77d57d84e13). This policy only scans the target subscriptions but does not make any additional evaluation. It leaves the chance to users to change the compliance results for each target subscription.
Following is a custom policy example to explain how to use the manual effect and what is the result.
- Policy definition with manual effect
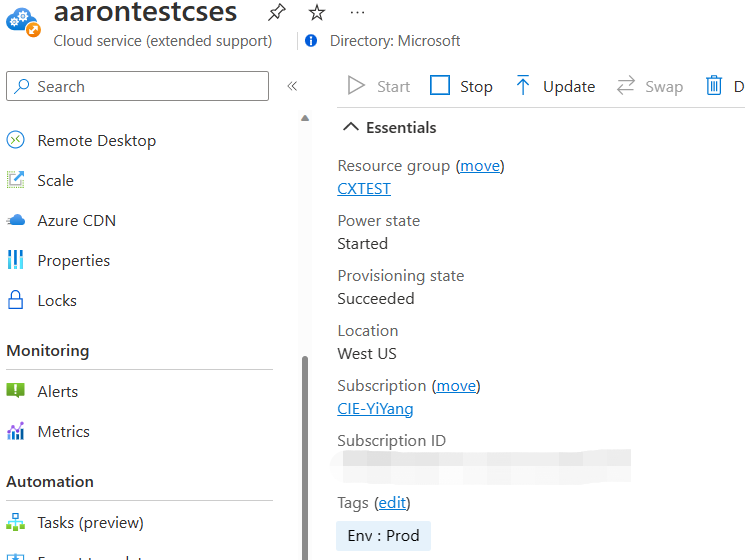
To illustrate the whole steps clearly, I created a custom policy which is checking the cloud services with “Prod” tag value. I set this custom policy with manual effect whose defaultState value is “Unknown”.
{
"mode": "Indexed",
"policyRule": {
"if": {
"allOf": [
{
"field": "[concat('tags[', parameters('tagEnvName'), ']')]",
"equals": "Prod"
},
{
"field": "type",
"equals": "Microsoft.Compute/cloudServices"
}
]
},
"then": {
"effect": "manual",
"details": {
"defaultState": "Unknown"
}
}
},
"parameters": {
"tagEnvName": {
"type": "String",
"metadata": {
"displayName": "Env Tag",
"description": null
},
"defaultValue": "Env"
}
}
}
You also can use “Compliant” or “Non-compliant” as the defaultState. All applicable resources will be evaluated to the default state specified in the definition.
The following screenshot is the evaluation results after this policy was assigned to my subscription. You can see the cloud service with “Prod” tag is marked as “Unknown”, the defaultState mentioned with the manual effect.
- Create attestations by REST API
You need to create attestations for each resource to change the compliance results of a resource or scope targeted by a manual policy. Currently, you can only use REST API to do the operations with the attestation.
Attestations - REST API (Azure Policy) | Microsoft Learn
In this example, I tried to change this cloud service from the “Unknown” status to “Compliant” so I used the following REST API to achieve it.
Attestations - Create Or Update At Resource - REST API (Azure Policy) | Microsoft Learn
You need to fill in the target resource information and the required evaluation result in the request body. The completed parameter list and their explanation can be found in the above doc link.
Following is a sample request body to change the resource status from “Unknown” to “Compliant”.
{
"properties": {
"policyAssignmentId": "/subscriptions/xx",
"complianceState": "Compliant",
"expiresOn": "2023-06-15T00:00:00Z",
"owner": "the owner of this subscription/resource group/resource",
"comments": "Change one CSES to Compliant",
"evidence": [
{
"description": " Change one CSES to Compliant",
"sourceUri": "https://gist.github.com/contoso/9573e238762c60166c090ae16b814011"
}
],
"assessmentDate": "When this assessment will be triggered (UTC time)",
}
}
- Show the required compliance result
After the new assessment is completed, you will see the target resource has been changed to the required compliant result.