This post has been republished via RSS; it originally appeared at: Microsoft Tech Community - Latest Blogs - .
Scenario
Configure a Logic App (Consumption) with Azure Active Directory Open Authentication so that it can be called/invoked by an Azure Data Factory Web Activity via Managed Identity.
References
- Create a Web Activity in Azure Data Factory: Web Activity - Azure Data Factory & Azure Synapse | Microsoft Learn
- Select the Managed Identity Authentication for the Web Activity call in Azure Data Factory: Web Activity - Azure Data Factory & Azure Synapse | Microsoft Learn
- Create a Logic App with an HTTP Trigger: Call, trigger, or nest logic apps by using Request triggers - Azure Logic Apps | Microsoft Learn
Services Used
- Azure Logic Apps (Consumption)
- Azure Data Factory
Steps
(1/2) Logic App Setup
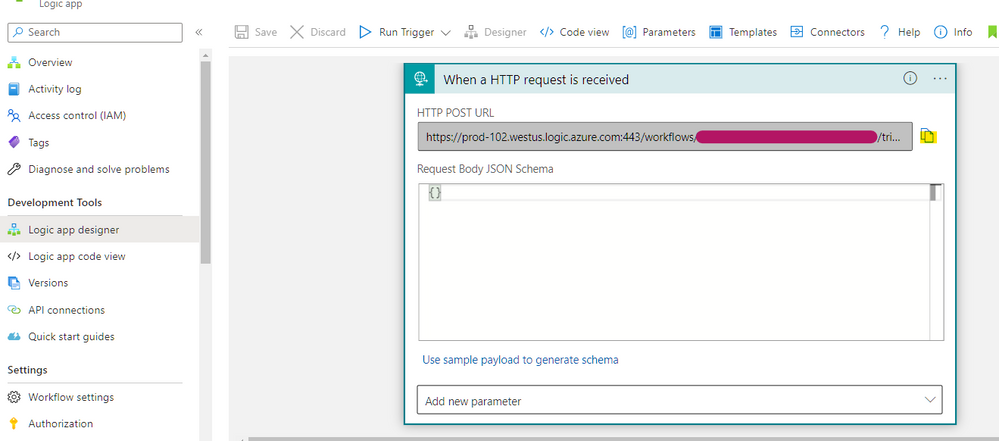
1. Create a Logic App with an HTTP Trigger: Call, trigger, or nest logic apps by using Request triggers - Azure Logic Apps | Microsoft Learn
a. Make a note of the callable endpoint / webhook / trigger URL
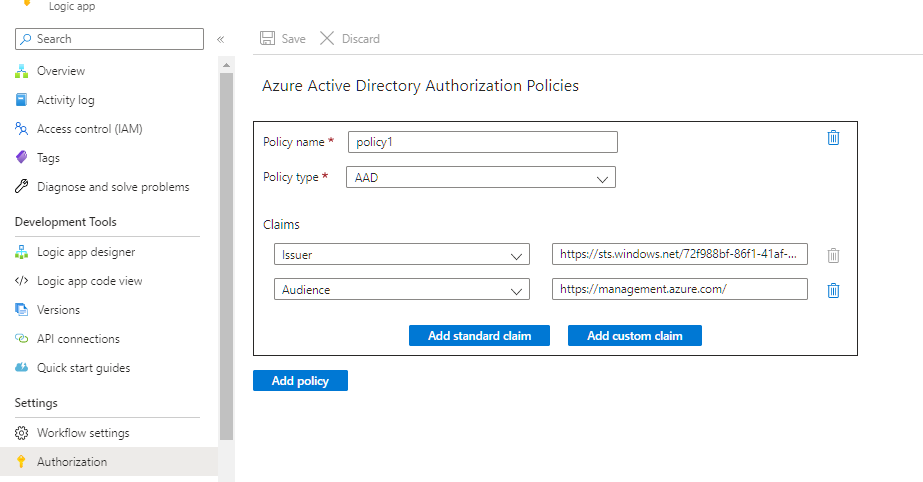
2. On the Logic App, go to Authorization and add the Authorization Policy in the Logic App: Secure access and data - Azure Logic Apps | Microsoft Learn
| Policy | [Policy Name] | |
| Policy Type | AAD | |
| Claims |
Issuer |
https://sts.windows.net/[Tenant ID]/ |
|
Audience |
||
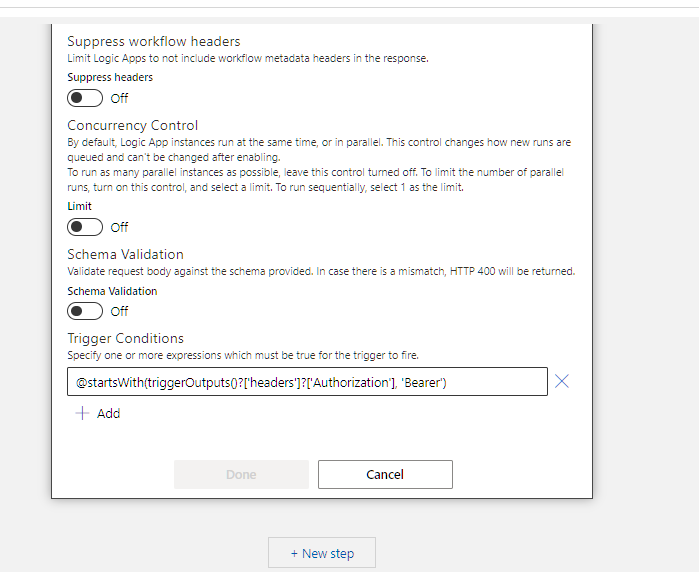
3. Add the Trigger Condition: Secure access and data - Azure Logic Apps | Microsoft Learn
- On the trigger, add the following Trigger Condition: @startsWith(triggerOutputs()?['headers']?['Authorization'], 'Bearer')
4. Include ‘Authorization’ header in request trigger outputs: Secure access and data - Azure Logic Apps | Microsoft Learn
- Open Code View
- Add and set the operationOptions property to IncludeAuthorizationHeadersInOutputs
Final Code View of the Logic App Trigger:
"triggers": {
"manual": {
"conditions": [
{
"expression": "@startsWith(triggerOutputs()?['headers']?['Authorization'], 'Bearer')"
}
],
"inputs": {
"schema": {}
},
"kind": "Http",
"operationOptions": "IncludeAuthorizationHeadersInOutputs",
"type": "Request"
}
}
(2/2) Azure Data Factory Setup
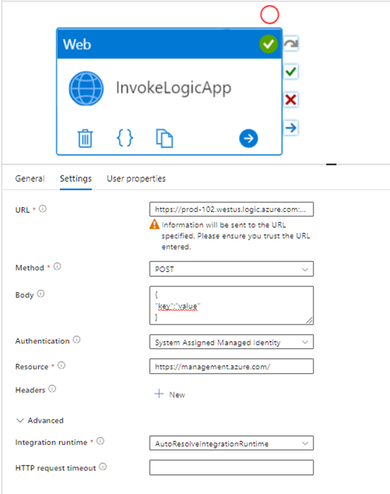
5. Create a Web Activity in Azure Data Factory: Web Activity - Azure Data Factory & Azure Synapse | Microsoft Learn
- Enter the following required values (along with additional optional parameters) on the Web Activity.
- Remove the SAS token when entering Logic App URL on the Web Activity to ensure it will not use SAS Token authentication during invocation.
| Property | Sample Value | Comments |
| URL | https://prod-[xx].[region].logic.azure.com:443/workflows/[Workflow ID]/triggers/manual/paths/invoke?api-version=2016-10-01&sp=%2Ftriggers%2Fmanual%2Frun&sv=1.0<removed> | Copied from Step 1a |
|
Method |
POST, GET… |
This can be changed on the Logic App trigger |
|
Body
|
Valid JSON |
|
|
Authentication |
System Assigned Managed Identity |
|
|
Resource |
Testing the Integration
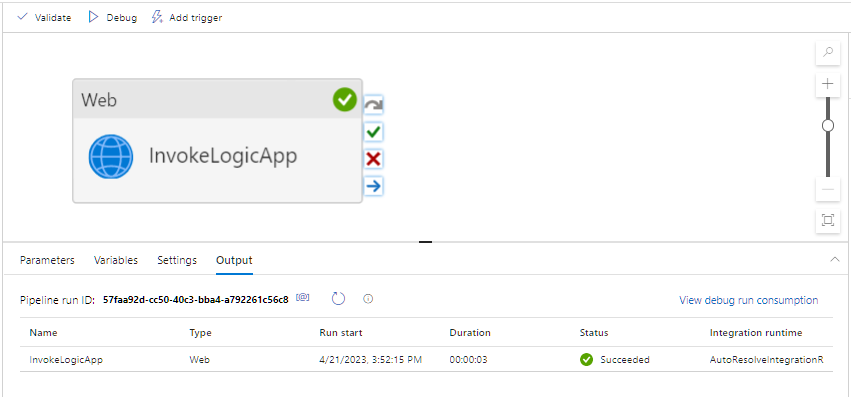
- Select Debug to test the pipeline and verify the Output shows a Succeeded status.
- Refresh your Logic App’s Run History for the latest invocation.