This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Community Hub.
This Blog applies to Microsoft Defender for Endpoint running on Windows Server OS Releases running SAP applications such as NetWeaver and S4Hana. The term “Defender” can refer to many different components and functionalities. Hereafter, “MDE” will refer to Microsoft Defender for Endpoint running on Windows Server. This article does not cover client desktops running SAPGUI or other frontend components.
Enterprise Security is a specialist role and the activities described in this blog should be planned in conjunction with the Enterprise Security Team. The objective of this blog is to provide the SAP Basis Team with a basic understanding of MDE on Windows and how to operate and troubleshoot problems with SAP Applications and MDE. It is generally recommended that the Enterprise Security Team coordinate with the SAP Basis Team and jointly design the MDE configuration, analyze any exclusions and scan scheduling.
Before continuing it is strongly recommended to watch the video in the link below. Microsoft Defender for Endpoint (MDE) is one component in the set of Defender solutions Microsoft Defender for Endpoint | Microsoft Docs. MDE can be integrated with the Defender365 Portal and Microsoft Sentinel SIEM/SOAR solution.
Microsoft Security documentation and training - Security documentation | Microsoft Learn
This blog focuses on two subcomponents: Next-generation protection (AntiVirus) and Endpoint Detection and Response (EDR). Next-generation protection is an AntiVirus (AV) product like other AV solutions for Windows environments. Endpoint Detection and Response (EDR) detects, then blocks suspicious activity and system calls. The Microsoft Defender 365 solution incorporates many security components that are beyond the scope of this blog.
For information on Microsoft Defender for Linux please refer to SAP Applications and Microsoft Defender for Linux - Microsoft Community Hub. MDE for Linux is significantly different than the Windows version.
Microsoft and other security software vendors track threats and provide trend information. More information can be found here: Cyberthreats, viruses, and malware - Microsoft Security Intelligence.
SAP Support Statement on Microsoft Defender EDR and Other Advanced Threat Protection (ATP) Security Solutions
SAP provide basic level documentation for conventional file scan Anti-Virus solutions. Conventional file scan Anti-Virus solutions compare file signatures against a database of known threats. When an infected file is identified the Anti-Virus software will typically alert and quarantine the file. The mechanisms and behavior of file scan Anti-Virus solutions are reasonably well known and are predictable, therefore SAP support can provide a basic level of support for SAP applications interacting with file scan Anti-Virus software.
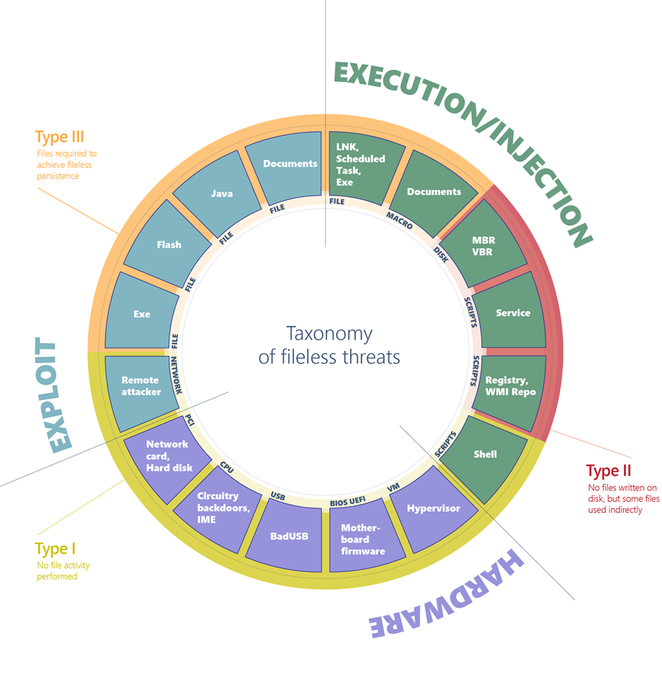
File based threats are now only one possible vector for malicious software. Fileless malware and that lives off the land, highly polymorphic threats that mutate faster than traditional solutions can keep up with, and human-operated attacks that adapt to what adversaries find on compromised devices. Traditional Anti-Virus security solutions are not sufficient to stop such attacks. Artificial intelligence (AI) and device learning (ML) backed capabilities, such as behavioral blocking and containment are required. Security software such as Defender for Endpoint EDR has Advanced Threat Protection (ATP) features to mitigate modern threats.
ATP security software is continuously monitoring Operating System calls such as file read, file write, create socket and other process level operations. When SAP software issues system calls and these system calls are blocked, delayed or quarantined this may cause general non-specific errors in SAP applications such as “Access Denied”.
SAP is not able to provide any level of support for EDR/XDR software as the mechanisms are adaptive, therefore not predictable and potentially are not reproducible. When problems are identified on systems running Advanced Security solutions SAP recommends disabling the security software and trying to reproduce the problem. A support case can then be raised with the security software vendor.
This blog deals solely with Microsoft Defender for Endpoint, but similar limitations apply to other solutions such as Trend Micro XDR, Symantec Endpoint Enterprise, McAfee and Crowdstrike. SAP Support policy is documented in 3356389 - Antivirus or other security software affecting SAP operations
Graphic showing structure of modern Fileless Threats
Top 10 Recommendations
- Limiting access to SAP servers, blocking network ports and all other common security protection measures remain an essential first step. The threat landscape has evolved from “file based” Viruses to file-less complex and sophisticated threats. Steps such as blocking ports and limiting logon/access to VMs is no longer considered sufficient to fully mitigate modern threats.
- Deploy Microsoft Defender to non-productive systems first before deploying to production systems. Deploying Microsoft Defender directly to production systems without testing is highly risky and has led to downtime
- To ensure that Microsoft Defender does not block disk IO the recommendation as of August 2023 is to disable Real Time Protection and schedule daily AntiVirus Scans
- MDE deployment should be a joint project between the SAP Basis Team and the Enterprise Security Team. The two teams need to create a phased deployment, testing and monitoring plan
- Use tools such as Perfmon (Windows) NMON or sysstat/KSAR (Linux) to create a performance baseline before deploying and activating MDE. Compare the performance utilization before and after activating MDE
- Deploy the latest version of MDE and use the latest releases of Windows, ideally Windows 2019 or higher. No testing has been done on old releases of Windows such as Windows 2012.
- Follow DBMS vendors recommendation for excluding files data and log files on DBMS servers
SQL Server – Configure antivirus software to work with SQL Server - SQL Server | Microsoft Learn
Oracle – See How To Configure Anti-Virus On Oracle Database Server (Doc ID 782354.1)
DB2 – https://www.ibm.com/support/pages/which-db2-directories-exclude-linux-anti-virus-software (use the same commands on Windows OS)
SAP ASE – contact SAP
MaxDB – contact SAP
- MDE Antivirus for SAP applications should have the following settings in most cases:
AntivirusEnabled : True
AntivirusSignatureAge : 0
BehaviorMonitorEnabled : True
DefenderSignaturesOutOfDate : False
IsTamperProtected : True
RealTimeProtectionEnabled : False
FullScanOverdue : False
- Tools such as InTune are recommended to ensure that the deployment, AV exclusions and configuration of MDE is consistently maintained
- Several new features are being implemented in MDE for Windows and these features have been tested with SAP systems. These new features reduce blocking and lower CPU consumption. It is recommended to use the very latest MDE for Windows release
Deployment Methodology
SAP and Microsoft do not recommend deploying MDE for Windows directly to all development, qas and production systems simultaneously and/or without careful testing and monitoring. Customers that have deployed MDE and other similar software in an uncontrolled manner without adequate testing have experienced system downtime as a result.
MDE for Windows and any other software or configuration change should be deployed into development systems first, validated in qas and only then deployed into production environments.
Using tools such as InTune to deploy MDE to an entire SAP landscape without testing is very likely to cause downtime.
The factors that need to be tested include:
- Disable Real Time Scanning and configure scheduled scans
- Exclude DBMS files and executables following DBMS vendor recommendation
- Analyze SAP TRANS_DIR, Spool and Job Log directories. If there are > 100,000 files consider archiving to reduce the number of files
- Confirm the performance limits and quotas of the shared file system used for SAPMNT. The SMB share source could be a NetApp appliance, a Windows server shared disk or Azure Files SMB.
- Configure exclusions such that all SAP application servers are not scanning the SAPMNT share simultaneously as this may overload shared storage server
- Interface files are recognized as an attack vector and it is generally recommend to host interface files on a dedicated non-SAP file server. Enable Real Time Protection on this dedicated file server. SAP Servers should never be used as file servers for interface files.
|
Note: some large SAP systems have more than 20 SAP application servers each with a connection to the SAPMNT SMB share. 20 application servers simultaneously scanning the same SMB server will likely overload the SMB server. It is recommended to exclude SAPMNT from regular scans. Typically the SMB server such as NetApp or the Windows SMB server will have built in AV scanning. If additional protection is required and scanning of the SAPMNT is configured, these scans should be configured on only one or two VMs only. Scheduled scans for SAP ECC, BW, CRM, SCM, Solution Manager and other components should be staggered to avoid all SAP components from overloading a shared SMB storage source shared by all SAP components. |
Frequently Asked Questions on Microsoft Defender for Endpoint
- What is “Microsoft Defender for Endpoint” (MDE)?
The term “Defender” can be used to refer to an entire suite of products and solutions. The term “Defender” is used across multiple products and technologies.
An overview of Microsoft 365 Defender is illustrated here What is Microsoft 365 Defender? | Microsoft Learn
- What are the MDE executable names and what is their purpose?
The two main processes that are often seen running on Windows Servers running SAP applications are MsMpEng.exe and MsSense.exe. If a SAP system or particular Windows Server has performance problems and any of the processes below are consuming large amount of CPU it is recommended to capture logs and open a case (see points 13 and 14 below)
|
MpCmdRun.exe |
Microsoft Defender Antivirus command-line utility |
|
MpDlpCmd.exe |
Microsoft Endpoint DLP command-line utility |
|
MsMpEng.exe |
Microsoft Defender Antivirus service executable |
|
ConfigSecurityPolicy.exe |
Microsoft Security Client Policy Configuration Tool |
|
NisSrv.exe |
Microsoft Defender Antivirus Network Realtime Inspection |
|
MsSense.exe |
Microsoft Defender for Endpoint service executable |
|
SenseCnCProxy.exe |
Microsoft Defender for Endpoint communication module |
|
SenseIR.exe |
Microsoft Defender for Endpoint Sense IR (Incident Response) module |
|
SenseCE.exe |
Microsoft Defender for Endpoint Sense CE (Classification Engine) module |
|
SenseSampleUploader.exe |
Microsoft Defender for Endpoint Sample Upload module |
|
SenseNdr.exe |
Microsoft Defender for Endpoint Sense NDR (Network Detection and Response) module |
|
SenseSC.exe |
Microsoft Defender for Endpoint Sense SC (Screenshot Capture) module |
|
SenseCM.exe |
Microsoft Defender for Endpoint Sense CM (Configuration Management) |
- How to check MDE Anti-Virus status?
Open a command prompt with Administrative rights and run these PowerShell commands
Get-MpComputerStatus
Get-MpPreference
- How to check Microsoft Defender Endpoint Detection and Response (EDR) status?
Click on the Windows Start Button and type “Windows Security” and open the Windows Security application. If there are any errors they will be highlighted on the main page of the Windows Security application. Note: many of the settings are centrally managed
Review events and errors using Event Viewer | Microsoft Learn
- How to check MDE software components are up to date?
MDE engine and signatures are updated via Windows Update. If MDE is not up to date or if there are errors in Windows Update contact the Security Team.
- How to update Defender Anti-Virus definitions?
Run Windows Update or the commands below
PS C:\Program Files\Windows Defender> .\MpCmdRun.exe -SignatureUpdate
Signature update started . . .
Service Version: 4.18.23050.9
Engine Version: 1.1.23060.1005
AntiSpyware Signature Version: 1.393.925.0
AntiVirus Signature Version: 1.393.925.0
Signature update finished.
PS C:\Program Files\Windows Defender>
Another option is:
PS C:\Program Files\Windows Defender> Update-MpSignature
- What is EDR Block Mode (AMRunningMode) and which running mode is recommended?
More information on EDR Block Mode can be found here Endpoint detection and response in block mode | Microsoft Learn and FAQ Endpoint detection and response (EDR) in block mode frequently asked questions (FAQ) | Microsoft Learn
This command will display the
Get-MPComputerStatus|select AMRunningMode
There are two modes: Normal and Passive Mode
Testing has only been completed with AMRunningMode = Normal for SAP systems. Further testing will be done in the future with 3rd party AV solutions and AMRunningMode = Passive Mode.
- What is Behavior Monitoring?
More information on Behavior Monitoring can be found:
Behavioral blocking and containment | Microsoft Learn
Check the configuration parameters BehaviorMonitorEnabled
- What is the recommended setting for RealTimeProtectionEnabled?
The current recommendation for MDE for Windows and MDE for Linux is to switch off Real Time Scanning and to schedule a scan during off peak times.
- How to configure Antivirus (AV) exclusions?
It is recommended that the SAP Basis Team coordinate exclusions with the Security Team. Exclusions should be configured centrally and not at the VM level.
Exclusions such as the shared SAPMNT file system should be excluded using the InTune admin tool.
AV exclusions - Set up exclusions for Microsoft Defender Antivirus scans | Microsoft Learn
To display configured exclusions run this command
Get-MpPreference | Select-Object -Property ExclusionPath
- How to configure Endpoint Detection and Response (EDR) exclusions?
It is not recommended to exclude files, paths or processes from EDR as this comprises the protection from modern non-file based threats. If required open a support case with Microsoft Support via the Defender365 Portal specifying executables and/or paths to exclude.
- Does MDE for Windows scan network shares?
By default MDE for Windows does scan SMB shared network file systems (for example a Windows server share \\server\smb-share or a NetApp share)
By default MDE for Linux does not scan NFS file systems.
- How to completely disable MDE for Windows for testing purposes?
MDE should be configured with “Tamper protection”. To disable MDE to isolate problems it is recommended to use troubleshooting mode https://learn.microsoft.com/en-us/microsoft-365/security/defender-endpoint/enable-troubleshooting-mode?view=o365-worldwide
To shutdown various subcomponents of the MDE AV solution run the following commands:
%programfiles%\Windows Defender\MpCmdRun.exe\MpCmdRun.exe -tpstate -off
Set-MpPreference -DisableRealtimeMonitoring $true
Set-MpPreference -DisableBehaviorMonitoring $true
Set-MpPreference -MAPSReporting Disabled
Set-MpPreference -DisableIOAVProtection $true
Set-MpPreference -EnableNetworkProtection Disabled
It is not possible to switch off EDR subcomponents. The only way is to completely off-board a device: https://learn.microsoft.com/en-us/microsoft-365/security/defender-endpoint/configure-endpoints-script?view=o365-worldwide#offboard-devices-using-a-local-script
It is not recommended to disable security software unless there is no alternative to solve or isolate a problem.
Turn Off Cloud-delivered Protection - Microsoft Advanced Protection Service (MAPS)
PowerShell Set-MpPreference -MAPSReporting 0
Or;
PowerShell Set-MpPreference -MAPSReporting Disabled
Cloud protection and sample submission at Microsoft Defender Antivirus | Microsoft Learn
Some customers may not wish to configure "Automatic sample submission” due to security policies.
- MDE Client Analyzer Support tool
Download the Microsoft Defender for Endpoint client analyzer | Microsoft Learn The latest released version of the tool can be found https://aka.ms/MDEAnalyzer
Performance analyzer for Microsoft Defender Antivirus | Microsoft Learn
- Where to open a support case?
Contact Microsoft Defender for Endpoint support | Microsoft Learn
Contact Microsoft Defender for Endpoint support
Learn how to contact Microsoft Defender for Endpoint support
- While testing MDE in Development and QAS VMs is it possible to delay the MDE extension deployment to Production SAP VMs if Defender for Cloud is activated? Is it possible to selectively deploy MDE VMs by Resource Group or other criteria?
By default Defender for Cloud deploys the MDE extension to all VMs in a subscription. Even one VM in a subscription that does not have MDE deployed can be used as an attack vector. If additional time is required to test MDE before deploying to production contact Microsoft Support via Defender365 portal.
Links
Supported Microsoft Defender for Endpoint capabilities by platform | Microsoft Learn
What's new in Microsoft Defender for Endpoint | Microsoft Learn
Behavioral blocking and containment | Microsoft Learn
Use the command line to manage Microsoft Defender Antivirus | Microsoft Learn
It is recommended to use Microsoft Intune to configure MDE for Linux and Windows
Manage Microsoft Defender for Endpoint using Intune | Microsoft Learn
Test MDE with a simulated attack including a file-less attack
Experience Microsoft Defender for Endpoint through simulated attacks | Microsoft Learn
Behavioral blocking and containment | Microsoft Learn
Behavioral blocking and containment
Learn about behavioral blocking and containment capabilities at Microsoft Defender for Endpoint
Client behavioral blocking | Microsoft Learn
2055193 - SUM file access denied due to antivirus - SAP for Me
3049164 - Using antivirus software with SAP HANA STUDIO - SAP for Me
3186509 - How can I enable antivirus scanning for uploaded files? - SAP for Me
1730930 - Using antivirus software in an SAP HANA appliance - SAP for Me
106267 - Virus scanner software on Windows - SAP for Me
1730997 - Unrecommended versions of antivirus software - SAP for Me
2543437 - 5 second delay in Enqueue requests with Antivirus software on Windows - SAP for Me
2088726 - Antivirus Software Causing Issues with Application Functionality - Platform - SAP for Me
1600271 - What are the required/recommended Antivirus exceptions for BPC? - BPC MS - SAP for Me
3158904 - Does Object Store Service on SAP BTP support Antivirus scanning - SAP for Me