This post has been republished via RSS; it originally appeared at: Microsoft Tech Community - Latest Blogs - .
If you are using Azure Storage to host your website, you might want to enable HTTPS Only to ensure secure communication between the client and the server. However, setting up a custom domain with HTTPS Only enabled can be a bit tricky. In this blog, we will guide you through the step-by-step process of setting up a custom domain for your Azure Storage account with HTTPS Only enabled.
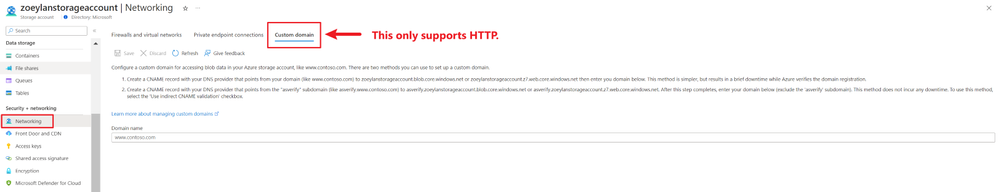
Firstly, I would like to briefly explain that currently, configuring a custom domain directly on Azure Storage is only supported for HTTP. If HTTP access is allowed, you can follow this official documentation for configuration: https://learn.microsoft.com/en-us/azure/storage/blobs/storage-custom-domain-name?tabs=azure-portal#map-a-custom-domain-with-only-http-enabled
Otherwise, if we need to use a custom domain with HTTPS Only enabled, we need to leverage other resources on Azure to do request forwarding. We will explore three options for setting up a custom domain in this scenario. These three options have their own pros and cons, and a brief comparison will also be provided at the end of the blog. You can choose to use either of them according to your specific situation.
- Azure CDN
- Application Gateway
- Azure Front Door
Please note that if you use either request forwarder, you no longer need to manually add the custom domain to storage. If you add the custom domain in this case, you may get "cannot verify" error.
Option 1: Using Azure CDN
Official Document Reference: https://learn.microsoft.com/en-us/azure/storage/blobs/storage-custom-domain-name?tabs=azure-portal#using-azure-cdn
If you have your own DNS provider already, you can ignore the first four steps and start with Step 5.
[Step 1]
First of all, you should get a domain. On Azure, you can deploy “App Service Domain” which will create a DNS zone for you automatically.
 |
 |
[Step 2]
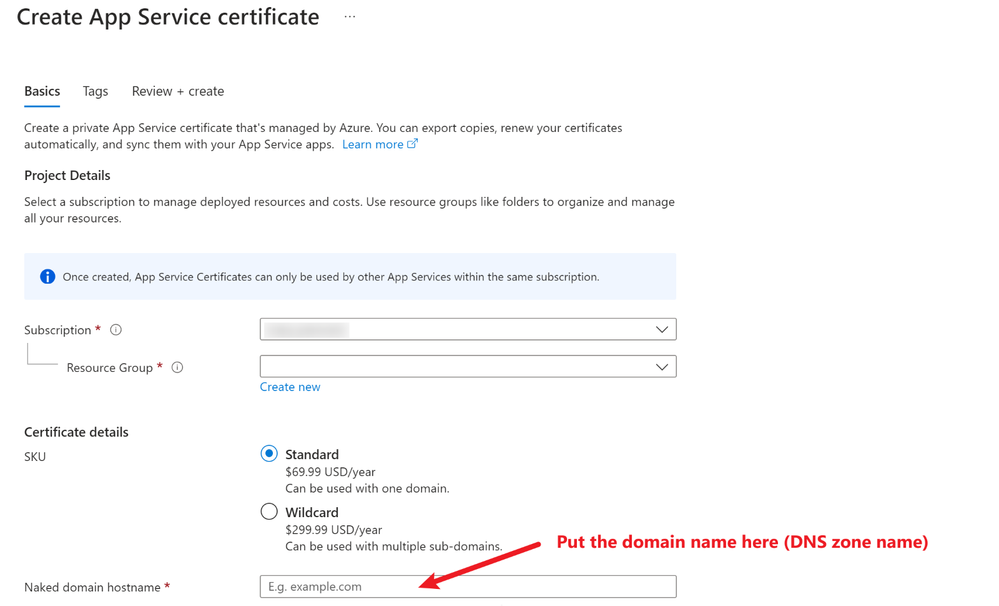
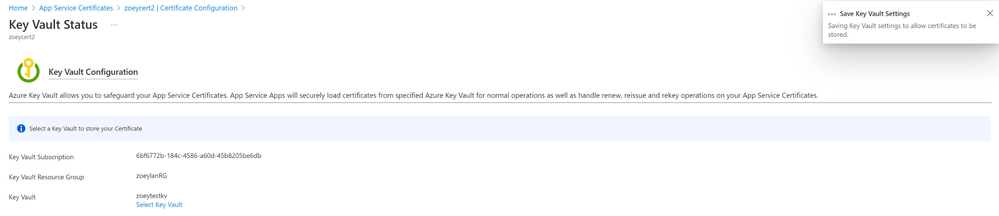
You need to purchase a certificate and create a key vault (if you have any existing KVs, you can use an existing one).
 |
|
After the Key Vault is created, you need to go to the Access configuration of the KV and update it to “Vault access policy”.
[Step 3]
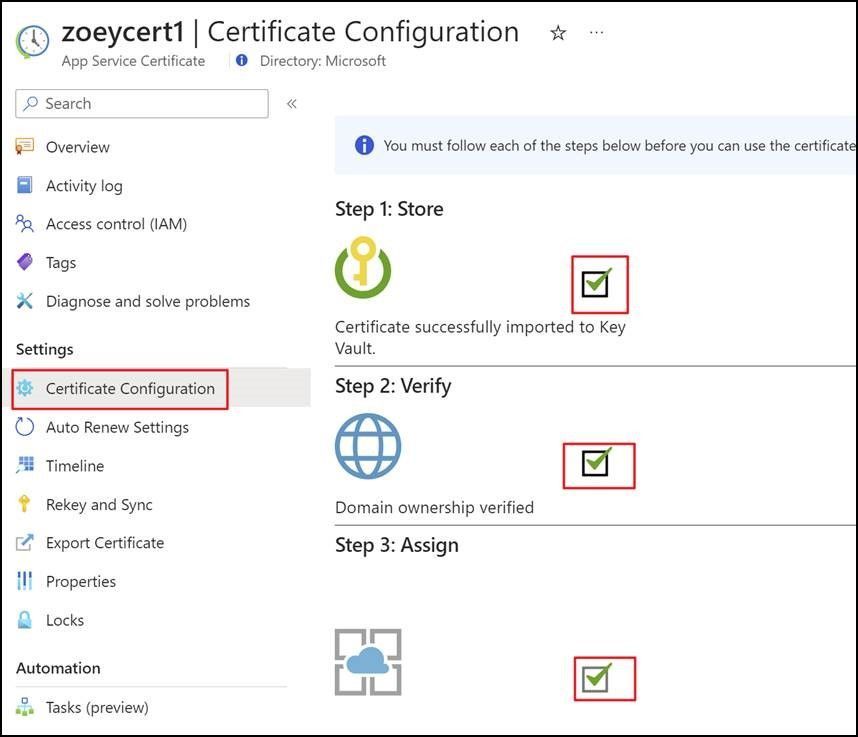
You need to go to the certificate that you just created. Then, you click the Certificate Configuration and have three boxes checked one by one.
a. You select the key vault you just created to link with the certificate.
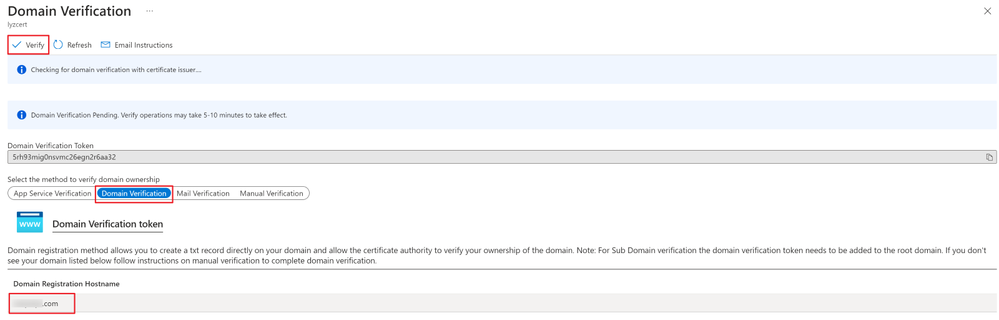
b. You verify the domain you created earlier.
This step may take a few minutes to take effect after checking for domain verification with certificate issuer.
[Step 4]
Now, you can add a CNAME record in your DNS zone, like below.
[Step 5]
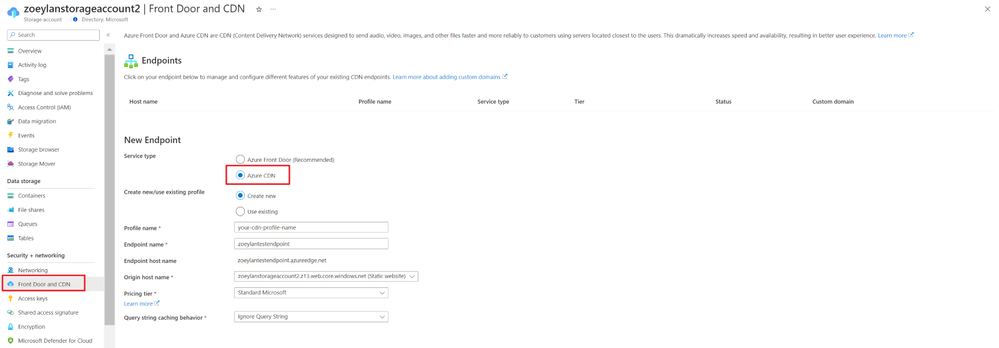
You can create a new CDN profile on Azure if you don’t have one already. This step is within your storage account, where you can navigate to "Front door and CDN" in the left-hand menu.
[Step 6]
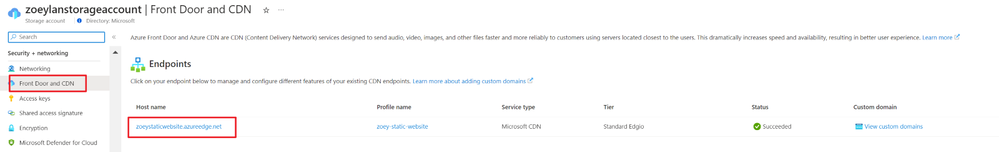
Then, you should be able to add a custom domain in your Endpoint of CDN.
[Step 7]
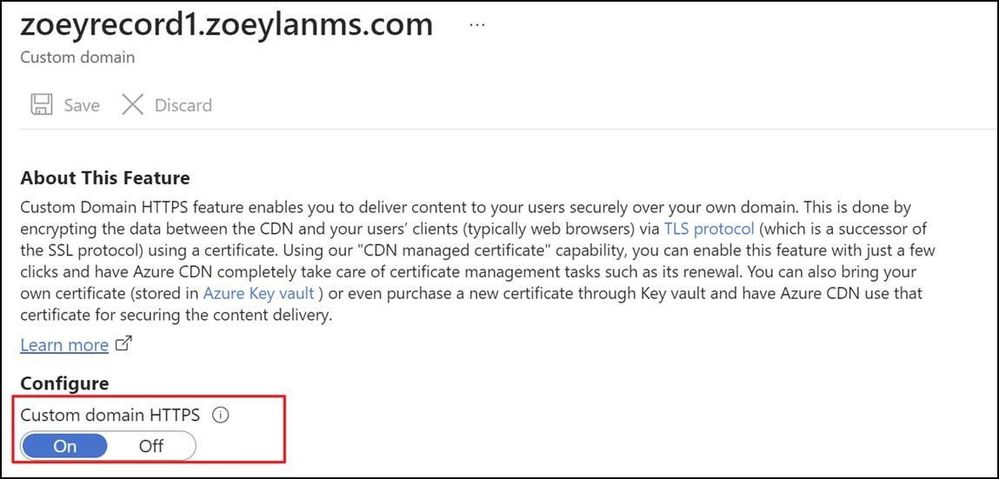
You need to enable the HTTPS feature for custom domain, you can click in the custom domain you just added in Step 6 and enable the HTTPS. (This process may take up to a few hours to finish.)
To sum up, the traffic is going from external hostname (CNAME record name you added in Step 4: in my example, it’s xxxxx.zoeylanms.com) to CDN (xxxx.azureedge.net), and finally reaching Storage account (static website).
Option 2: Using Application Gateway
This option is similar to the first one, but instead of using Azure CDN to transfer requests, we will use Application Gateway to act as a web traffic load balancer and provide advanced security features. Here are the steps to set up Application Gateway:
Step 1-3 in Option 1 are still needed if you don’t have your DNS provider.
[Step 4]
You need to have an Application Gateway resource on Azure. You could follow our official document to create an Application Gateway on Azure Portal: https://learn.microsoft.com/en-us/azure/application-gateway/quick-create-portal
Note: The backend protocol used in the document example is HTTP. We can update it to HTTPS in later step.
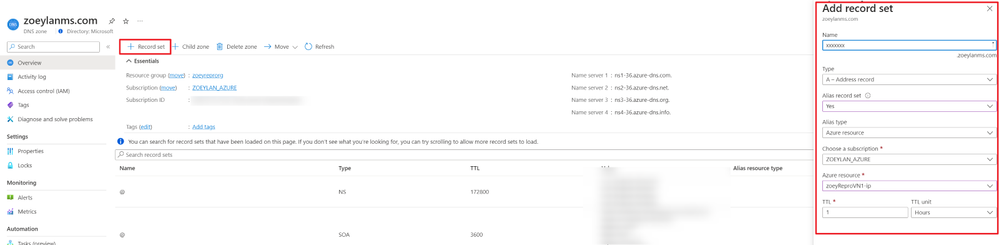
[Step 5]
You can check the public IP of the Application Gateway you just created first.
Then, you need to go back to the DNS zone you created earlier and add a new A record to map traffic to the Application Gateway using the public IP.
[Step 6]
You open the Application Gateway, go to the Backend Pools, and click the backend pool created just now. For the Target Type, you should pick "IP address or FQDN" and then put the static web site endpoint in the Target.
Format: xxxxx.z7.web.core.windows.net
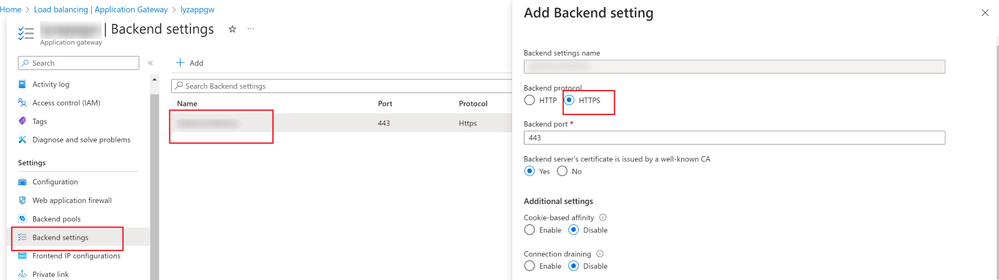
[Step 7]
In the Backend Settings, you should make sure the Backend protocol is updated to “HTTPS”.
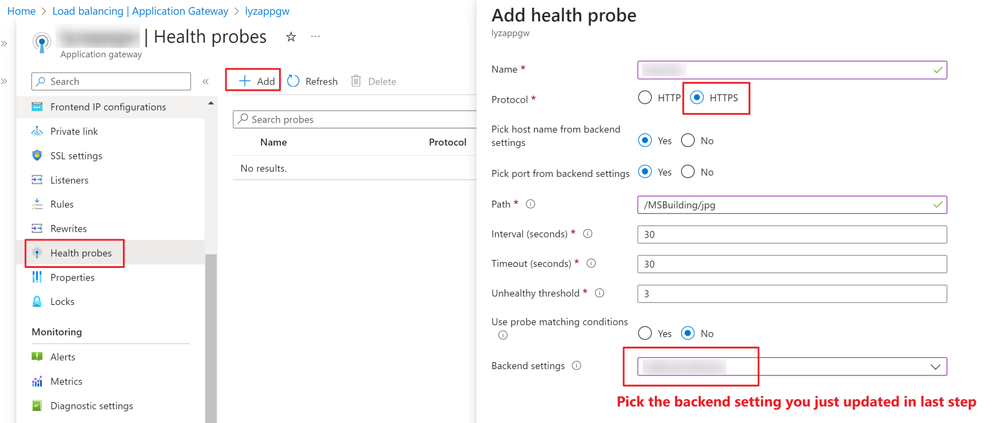
[Step 8]
Then, you can create a custom health probe with a protocol in HTTPS like below to monitor the health of the resources in the backend pool.
[Step 9]
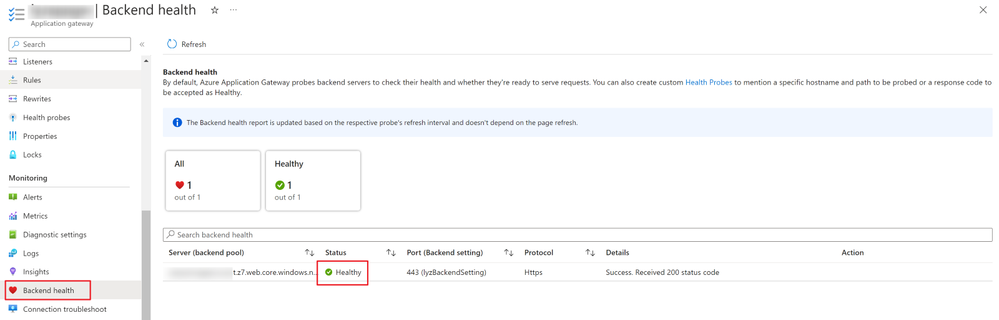
Before you save the new health probe, there is a test showing the connection result. Meanwhile, you can also check the backend health like the screenshot below later.
Option 3: Using Azure Front Door
Configuring request forwarding using Front Door is very similar to Azure CDN. You can follow our official documentation to complete the deployment.
Comparison
|
Option |
Azure CDN |
Application Gateway |
Azure Front Door |
|
Behavior in custom domain setting |
Azure CDN does not have a built-in option for force HTTPS redirection. In this scenario, when accessing the website through a custom domain using HTTP, you will receive a 400 error with the error message 'AccountRequiresHttps'. However, everything works normally when accessing the webpage through a custom domain link using HTTPS. |
The scenarios that can be achieved with Application Gateway are more flexible because we can configure and combine the listener's protocol and backend setting's protocol separately. Therefore, whenever client accesses through either HTTP or HTTPS, by configuring the backend setting, we can forward requests to the backend storage account using HTTPS. |
Azure Front Door does have a built-in option for force HTTPS redirection. This can be configured in the Front Door's routing rules by selecting “Redirect all traffic to use HTTPS”. When a user tries to access the website using HTTP, Front Door will automatically redirect the request to HTTPS. |
|
Pricing |
Outbound data transfers are billed based on the node location from where the transfers are served, not the end user’s location.
Reference:
|
The cost of Application Gateway is mainly composed of fixed and variable charges. The fixed charge is based on a fixed hourly rate (which may vary by region), while the variable charge depends on the number of capacity units, with an hourly price for each capacity unit.
Reference: |
Each part of the request process is billed separately:
Reference: |
|
Performance |
Azure CDN offers global content delivery with low latency and high throughput. It stores cached content on the edge servers’ POP locations that are close to consuming users, thereby minimizing network latency.
Reference: |
Application Gateway provides layer 7 load balancing and web application firewall (WAF) capabilities, offers advanced traffic management features such as session affinity, redirection, and URL-based routing. It provides centralized management and monitoring of multiple backend servers.
Reference:
|
Azure Front Door provides global load balancing and routing of traffic to different backend services. It unified static and dynamic delivery offered in a single tier to accelerate and scale your application through caching, SSL offload, and layer 3-4 DDoS protection.
Reference:
|
To summarize the blog, the most important thing to remember is that Azure Storage currently does not support the HTTPS Only + Custom domain mode. Therefore, we need to leverage a resource that can perform request forwarding to achieve our goal. In the previous sections, we introduced three of the most commonly used resources: Azure CDN, Application Gateway, and Azure Front Door.