This post has been republished via RSS; it originally appeared at: Microsoft Tech Community - Latest Blogs - .
A huge thank you to Alex Jercaianu, Justin Sapp, Kosi Nwabueze, and Milan Justel for implementing this feature!
Discovery of Network-designated Resolvers (DNR) is an upcoming IETF standard to discover encrypted DNS servers. Before DNR, devices getting DNS server from their local network would not be able to use encrypted DNS without manually finding out the IP address of their desired encrypted DNS server and configuring it on client-side. DNR enables devices to use encrypted DNS protocols like DNS over HTTPS (DoH) and DNS over TLS (DoT) on the client-side without requiring manual endpoint configuration.
We are excited to announce client-side DNR support in Windows Insiders build 25982 and higher!
How does client-side DNR work?
Let us look at what happens when a machine with client-side DNR enabled attempts to join a new network. First, the machine queries the local DHCP server to acquire an IP address. During that query it also requests special DNR-specific options (OPTION_V4_DNR for DHCPv4 or OPTION_V6_DNR for DHCPv6). The local DHCP server which is running server-side DNR responds to the machine with all the required information for configuring encrypted DNS such as the IP address of the encrypted DNS server, list of supported encrypted DNS protocols, their port numbers, and server authentication information. On receiving this information, the client machine sets up an encrypted DNS tunnel automatically with the server discovered through DNR.
From the user’s perspective, they joined a new network as they normally would and without any effort on their part, they are reaping the benefits of encrypted DNS!
How to use DNR on Windows Insider builds?
First step is to install the latest Windows Insider build (25982 or higher). DNR support is not available on non-Insider Windows builds yet.
Once a compatible Windows Insider build is installed, a new registry key needs to be created to enable DNR on the device.
Please note: You should proceed with the deployment steps below only if you have prior experience with modifying registry. This is NOT recommended for people who are unfamiliar with registry keys.
UI
The registry key can be created using UI by the following steps:
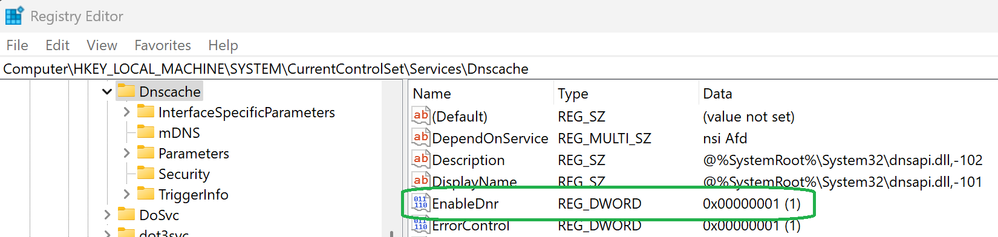
- Open Registry Editor on your Windows device
- Navigate to “Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Dnscache”
- Click on “Edit” -> “New” -> “DWORD (32-bit) Value” (on the top left side of the window)
- Rename this new registry key from “New Value #1” to “EnableDnr”
- Double-click on “EnableDnr” registry key
- In the new pop-up window, verify value name is “EnableDnr” and set value data to “1”
- Click “OK”
Command prompt
Alternatively, the following command can be run in an administrator command prompt:
reg add HKLM\SYSTEM\CurrentControlSet\Services\Dnscache\Parameters /v EnableDnr /t REG_DWORD /d 1
After all the registry changes are done, reboot the device for the new settings to take effect.
To see DNR working in action, try joining a network whose DHCPv4 or DHCPv6 server supports server-side DNR.
During our internal testing, we partnered with BT Group who prototyped server-side DNR on their DHCPv4 servers. A Windows Insiders device with DNR enabled was joined to a network provisioned by BT. The Windows Insiders device was able to use OPTION_V4_DNR to discover, validate and use BT’s trial DNS over HTTPS service.
Please note that our current client-side DNR implementation only supports configuration through following modes as stated in the DNR IETF draft:
- DHCPv4 without support for ADN only mode.
- DHCPv6 without support for ADN only mode and only accepts one instance of OPTION_V6_DNR.
We do not support the IPv6 RA Encrypted DNS option yet.
To stop using client-side DNR, the following command can be run in an administrator command prompt:
reg add HKLM\SYSTEM\CurrentControlSet\Services\Dnscache\Parameters /v EnableDnr /t REG_DWORD /d 0
After running the command, reboot the device to return the machine to its original state.