This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Community Hub.
Introduction
In the dynamic landscape of software development, developers across diverse organizations are embracing a wide variety of Source Code Management (SCM) and CI/CD pipeline systems to optimize their workloads. While this trend presents flexibility, collaboration, and speed to software development, the challenges of securing the application lifecycle become increasingly complex. As organizations strive to improve security posture by embedding security and compliance capabilities from code to cloud, having a unified and robust platform to help manage and prioritize security signal becomes paramount.
At Microsoft Ignite 2023, Microsoft Defender for Cloud unveiled a new integration, extending its DevOps security coverage outside of the Microsoft ecosystem and integrating with the all-in-one DevOps platform GitLab. With this integration, security practitioners can monitor the security posture of their GitLab environments and kick off developer remediation workflows. Additionally, customers with Defender CSPM will receive advanced contextualization and prioritization capabilities for their GitLab environments.
Note: The initial Public Preview for GitLab only supports Ultimate users with GitLab SaaS.
Improving your GitLab Security Posture with Defender for Cloud
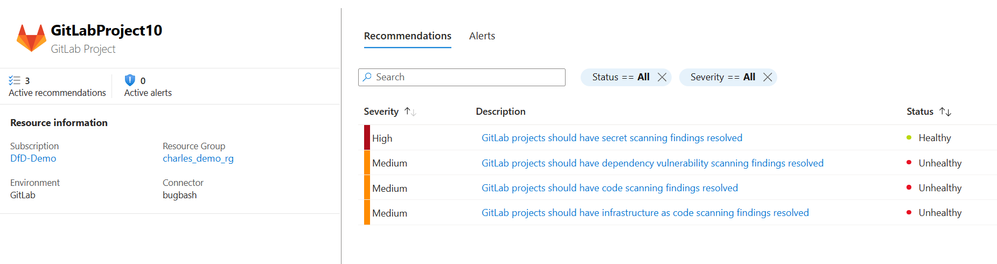
As Defender for Cloud extends its DevOps security posture management coverage to include GitLab, we are excited to announce that we will ingest findings from GitLab Ultimate that are designed to help you understand and mitigate risks discovered in your GitLab projects, including:
- Exposed secrets: discover and resolve plaintext secrets stored in code.
- Vulnerable dependencies: proactively review and address vulnerabilities discovered in open-source dependencies.
- Code weaknesses: get insight into issues discovered in code scans to strengthen the security of your applications.
- Infrastructure-as-Code misconfigurations: address findings within infrastructure-as-code templates prior to runtime.
These findings include in-depth security risk insights, actionable remediations steps, and clear identification of the weaknesses and vulnerabilities within specific projects and CI/CD pipelines.
From Defender for Cloud recommendations, security practitioners can trace back to the file and developer that introduced the vulnerability.
Beyond these, Defender CSPM customers have access to advanced pre-breach threat hunting for GitLab environments through the Cloud Security Explorer. Customers can leverage the Cloud Security Explorer to build targeted queries to identify GitLab projects with the highest business risk, such as projects that are publicly accessible and contain a plaintext secret or projects that have source code with remote code execution vulnerabilities.
As an example, the image below shows how we can identify all GitLab projects that contain a high severity CVE in a dependency package being implemented by application developers.
From there, you can quickly identify the project URL to trace back to the developer owner.
More contextualized insights will continuously be added for GitLab to better prioritize your security findings and breach exposure using cloud environment context.
Onboarding your GitLab Environment to Defender for Cloud
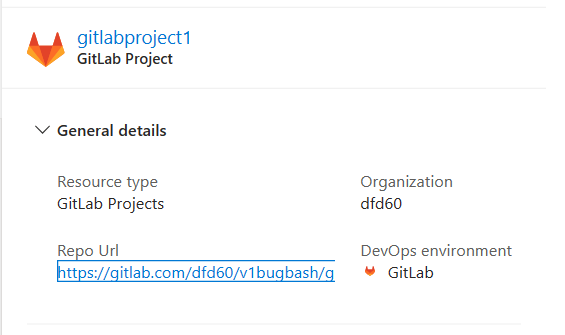
To onboard your GitLab environment to Defender for Cloud, simply navigate to Environment Settings > Add environment and select GitLab.
From there, authorize your GitLab account credentials and create your connector. Defender for Cloud will continuously auto-discover and monitor the projects and CI/CD pipelines created in your GitLab group to provide comprehensive coverage and mitigate critical risks. For more information, see the dedicated onboarding information here.
Summary
This blog announced the Public Preview of GitLab in Microsoft Defender for Cloud and the security posture management capabilities security teams receive when they onboard their GitLab environments.
More information