Azure Sentinel supports collecting telemetry from a wide array of Microsoft sources. Some of them are listed in the Sentinel’s connector page and documentation. However, Sentinel can collect logs from most Azure services, even when not listed above.
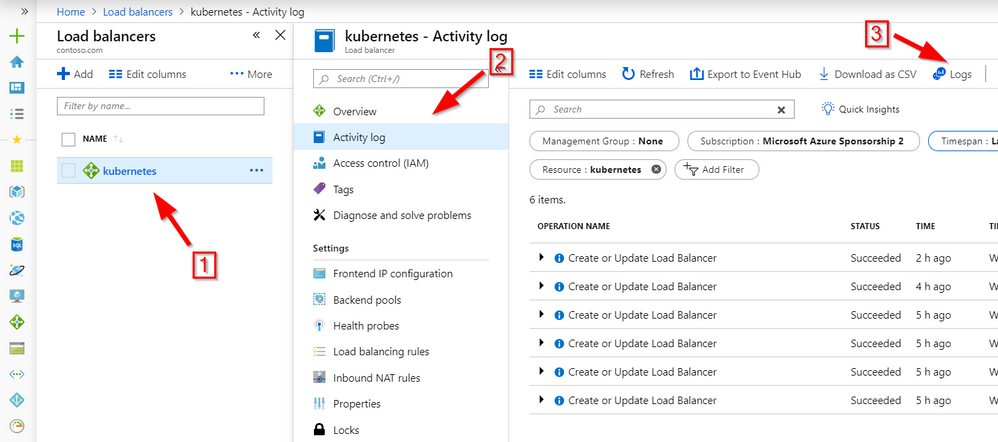
To log a service to Sentinel, pick the service (1), select “Activity log” from the menu (2), and then click the “Logs” button (3). Note that in this screen, before pressing “Logs” you can review the information that will be sent to Sentinel.
On the next screen, click “Add”, then “Select workspace” and select the Sentinel workspace.
In some cases, the service provides diagnostic telemetry but not audit logs. The diagnostic telemetry is usually geared towards operations rather than security monitoring but in most cases will be useful also for security monitoring. In such cases use “Diagnostic settings” instead of “Activity log” and select “Add diagnostic setting”.
You can find detailed further instructions for some services here. Note that some of them do not use the method outlined above:
- App Services and Web Application monitoring – goes beyond how to connect instructions and provides a reference architecture that can be extended from operational to security monitoring using Sentinel.
- Azure Activity – you can collect Azure Activity using the built-in connector, however it is recommended to connect through the subscription diagnostic settings in a similar manner the one described above. This will ensure lower latency and broader collection.
- Azure B2C – included as part of AAD events. Note that B2C, which is not part of a subscription, has to be linked to a subscription in the tenant in which Sentinel exists.
- Azure B2B – included as part of AAD events
- Application Insights: use queries across workspaces
- Azure DDOS
- Azure Databricks
- Azure Firewall, plus sample queries and a Sentinel dashboard
- Azure Front Door
- Azure Key Vault
- Azure Logic Apps
- Azure NSG:
- Azure SQL Audit log
- Azure Site Recovery
- Azure Storage
- Desktop Analytics – Just use your Sentinel workspace when configuring Desktop Analytics
- Intune
- Microsoft Cloud App Security
- Alerts and discovery logs are supported out of the box
- Use CEF for activity log as described here.
- Office 365 DLP alerts: supported as part of the built-in Office 365 connect. See details here.
- SCCM
- SQL Server