This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Through the rapidly growing adoption of open source databases, customers need to access the data and services privately and securely from their networks grow exponentially. We have been incrementally adding support for network isolation through Firewall rules followed by VNet Service endpoints. Today we are excited to announce the public preview of Azure Private Link support for the Azure database for PostgreSQL Single server.
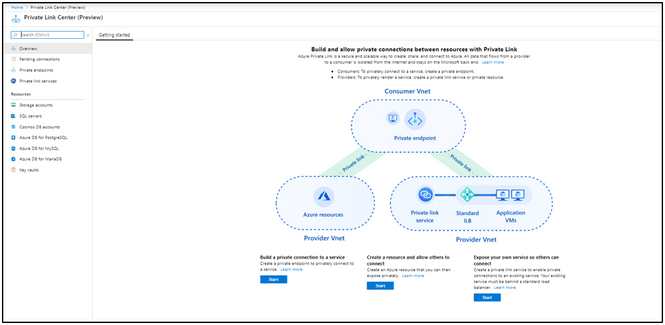
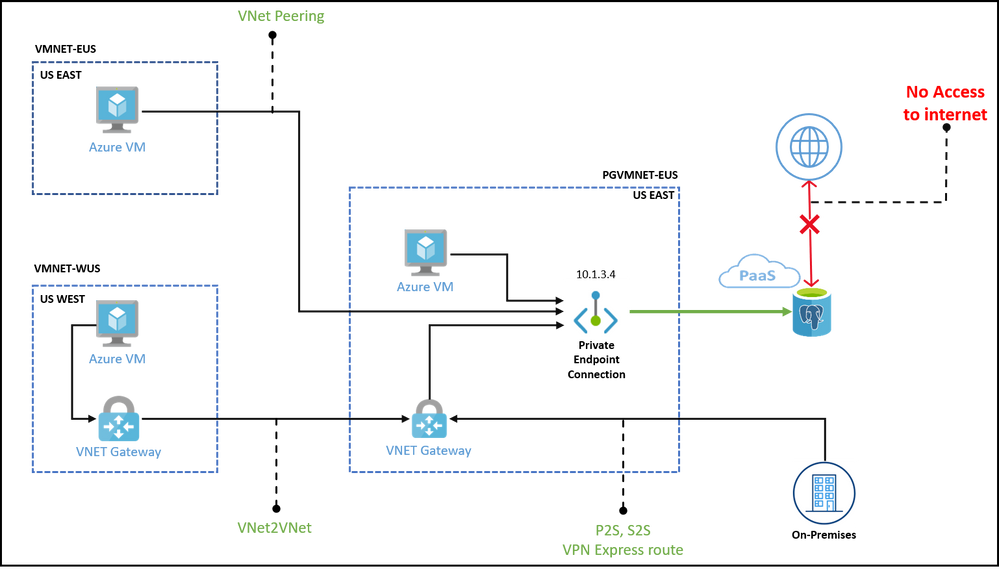
Azure Private Link is a secure and scalable way for Azure customers to consume Azure database for PostgreSQL Single server service privately from their Azure Virtual Network (VNet). The technology is based on a provider and consumer model where the provider and the consumer are both hosted in Azure. A connection is established using a consent-based call flow and once established, all data that flows between the service provider and service consumer is isolated from the internet and stays on the Microsoft network. There is no need for gateways, network address translation (NAT) devices, or public IP addresses to communicate with the service.
Azure Private Link essentially brings Azure services inside the customer’s private VNet. The PostgreSQL resources can be accessed using the private IP address just like any other resource in the VNet. This significantly simplifies the network configuration by keeping access rules private.
Benefits of using private link for Azure Database for PostgreSQL
- Data exfiltration protection: With Private Link for Azure Database for PostgreSQL - Single server, customers can now set up network access controls like NSGs to restrict access to the private endpoint. Individual Azure PaaS resources are then mapped to specific private endpoints. A malicious insider can only access the mapped PaaS resource (for example an Azure Database for PostgreSQL Single server) and no other resource.
- Private on-premises access: Since Azure Database for PostgreSQL Single server is mapped to private IP addresses in the customer’s VNet, they can be accessed via Azure ExpressRoute private peering. This effectively means that the data will traverse a fully private path from on-premises to Azure. The configuration in the corporate firewalls and route tables can be simplified to allow access only to the private IP addresses. With Private Link, customers can enable cross-premises access to the private endpoint using Express Route (ER), private peering or VPN tunnel. They can subsequently disable all access via public endpoint and not use the IP-based firewall.
- Simple to setup: Azure Private Link for Azure Database for PostgreSQL is simple to setup with minimal networking configuration needed. Connectivity works on an approval call flow and once a PostgreSQL resource is mapped to a private endpoint, the connectivity works out of the box without any additional configurations on route tables and Azure Network Security Groups (NSGs).
How to setup private link for Azure Database for PostgreSQL Single Server
We will learn how to setup a private link for your Azure Database for PostgreSQL and use a Azure VM to access it securely using the private link. We can use Portal or CLI to setup the private link. Here I have shown setting up private link using Azure portal.
Step 1:
- On the upper-left side of the screen in the Azure portal, select Create a resource > Networking > Private Link Center (Preview).
- In Private Link Center - Overview, on the option to Build a private connection to a service, select Start.
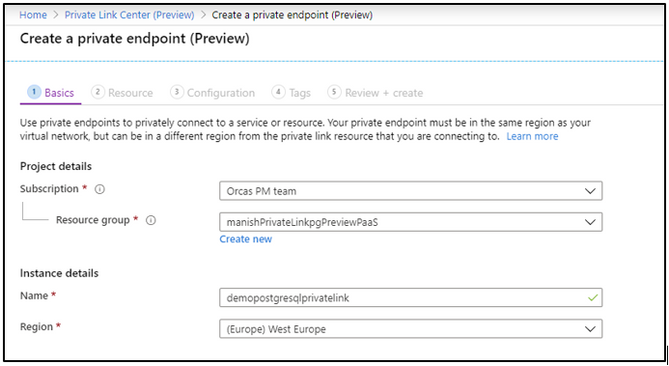
| Setting | Value |
| Project details | |
| Subscriptions | Select your subscription |
| Resource group | Select myResourceGroup. |
| INSTANCE DETAILS | |
| Name | Enter myPrivateEndpoint. If this name is taken, create a unique name |
| Region | Select RegionName |
Step 2: In Create a private endpoint (Preview) - Basics, enter or select this information:
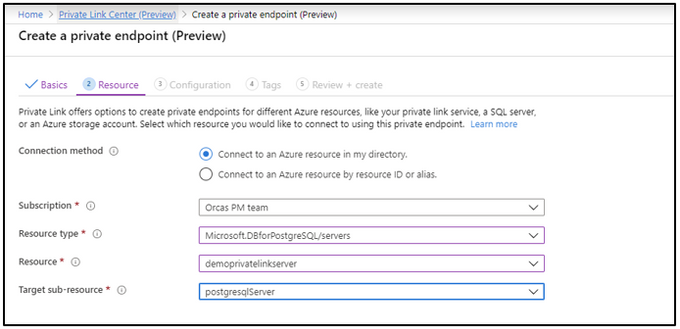
Step 3: Select Next: Resource. In Create a private endpoint - Resource, enter or select this information:
| Settings | Value |
| Connection method | Select connect to an Azure resource in my directory |
| Subscription | Select your subscription |
| Resource type | Select Microsoft.DBforPostgreSQL/servers |
| Resource | Select myServername |
| Target sub-resource |
Select postgresqlServer |
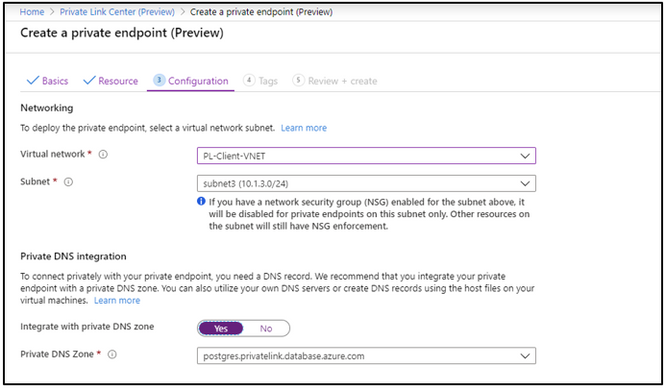
Step 4: In Create a private endpoint (Preview) - Configuration, enter or select this information
| Setting | Value |
| NETWORKING | |
| Virtual Network | Select MyVirtualNetwork |
| Subnet | Select mySubnet |
| PRIVATE DNS INTEGRATION | |
| Integrate with private DNS Zone | Select Yes |
| Private DNS Zone | Select (new) privatelink.database.azure.com |
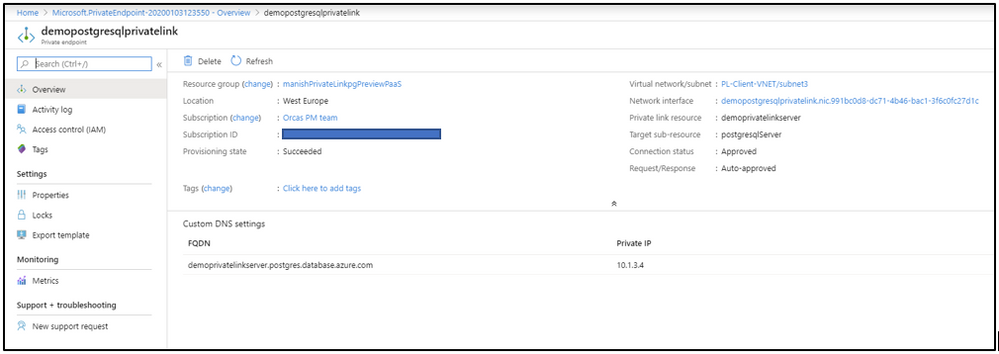
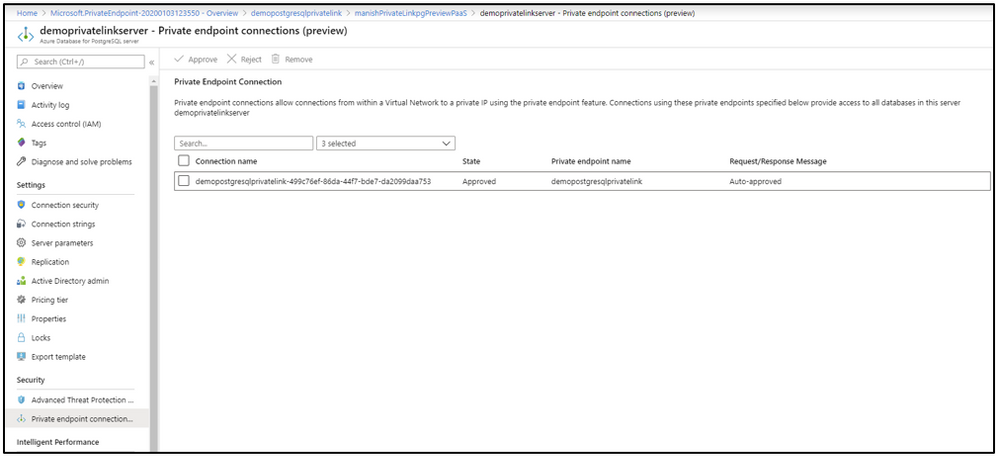
Step 5: Select Review + create. You're taken to the Review + create page where Azure validates your configuration. The private link overview shows the mapped PostgreSQL resource.
verify that the private link points to the PostgreSQL resource and the necessary resolution is happening.
PostgreSQL server private link
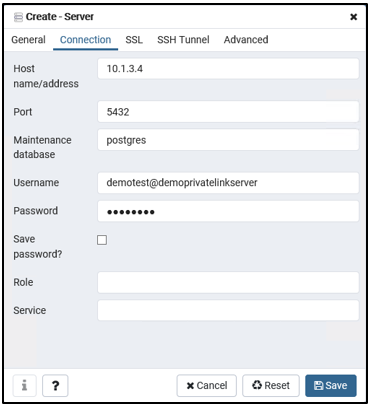
Now, in order to connect to the PostgreSQL resource, you can directly use the IP available (10.1.3.4) and provide the required credentials for the database server. In the example below I am using PGAdmin to connect to the database server.
You can also pass the server name in the host name field above demoprivatelinkserver.postgres.privatelink.database.azure.com
Learn More
You can find more details on the private link for Azure Database for PostgreSQL Single server here. You can give the Azure Private Link integration a try today. If you have questions, please reach out to the AskAzureDBforPostgreSQL@service.microsoft.com alias.