This post was in collaboration with
When it comes to incident management and response, time is everything. Impact and damage from a malicious actor can be weighed in minutes. Azure Sentinel strives to deliver a strong experience for users while also providing tools for investigations. Recently, a newer feature called Watchlists was released to pubic preview. This new feature can be utilized to speed up and drive investigations to be more efficient. This blog is going to provide examples of how they can be used while providing a scenario with examples.
What are Watchlists?
Watchlists are a list of details that are transformed into a log format for use within Azure Sentinel. The list can be made by uploading a CSV file of data or made via the Azure Sentinel API. The information uploaded can be details that are within the logs ingested into Azure Sentinel or can be external data used to enrich information within Sentinel. Watchlists can be used within Analytic Rules, Threat Hunting, Playbooks, and anything else that involves running queries.
Common scenarios for using watchlists include:
- Investigating threats and responding to incidents quickly with the rapid import of IP addresses, file hashes, and other data from CSV files. Once imported, users can use watchlist name-value pairs for joins and filters in alert rules, threat hunting, workbooks, notebooks, and general queries.
- Importing business data as a watchlist. For example, import user lists with privileged system access, or terminated employees, and then use the watchlist to create allow and deny lists used to detect or prevent those users from logging in to the network.
- Reducing alert fatigue. Create allow lists to suppress alerts from a group of users, such as users from authorized IP addresses that perform tasks that would normally trigger the alert, and prevent benign events from becoming alerts.
- Enriching event data. Use watchlists to enrich your event data with name-value combinations derived from external data sources.
An example of a Watchlist that can be used within Azure Sentinel would be a list of recently terminated employees that still have access and permissions to resources. To avoid the risk of insider threats, a Watchlist with the employees can be created and analytic rules can utilize the list to monitor for all activities that are related to the accounts. This use case ensures that the former employees are not active in any way that would be seen as malicious. Another example would be to make a list of IP ranges that are aligned with different office locations. This list of ranges would allow for checks to be done to make sure that IP’s that are being used to sign-in or connect to resources are within the ranges. If an IP is outside the ranges, an alert can be raised immediately for investigation.
———————————————————————
For additional use case examples, please refer to these relevant blog posts from our colleague:
Playbooks & Watchlists Part 1: Inform the subscription owner
Playbooks & Watchlists Part 2: Automate incident response
Please refer to our documentation for other additional details.
———————————————————————
How to create a watchlist?
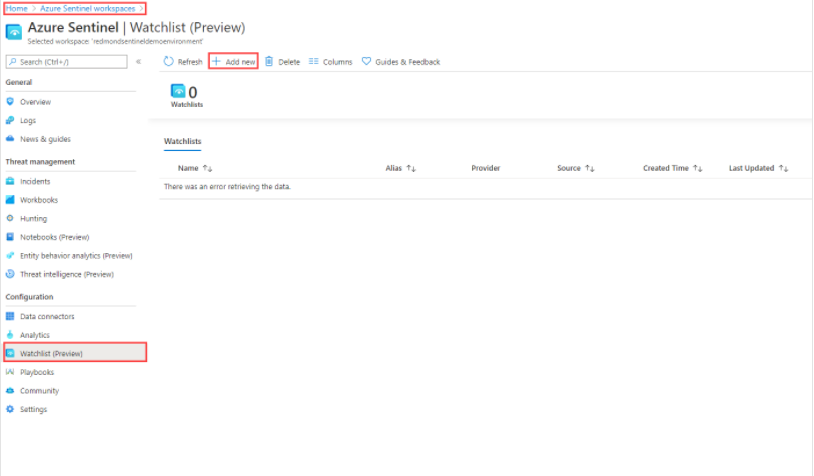
From the Azure portal, navigate to Azure Sentinel > Configuration > Watchlist and then select Add new.
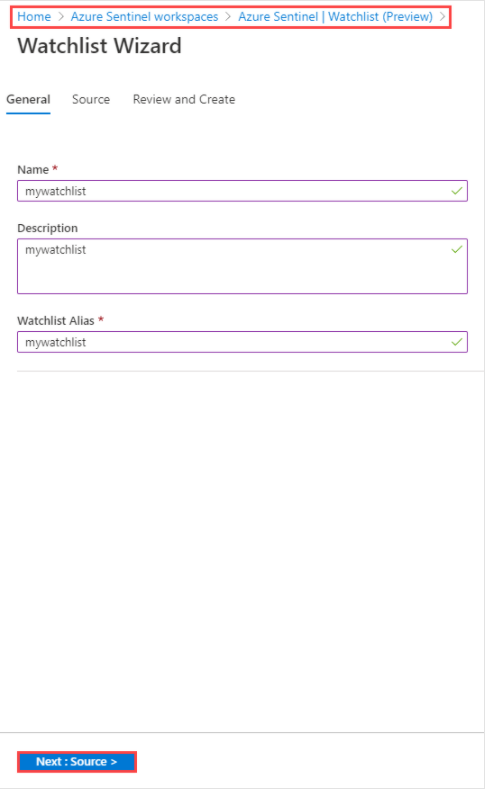
On the General page, provide the name, description, and alias for the watchlist, and then select Next.
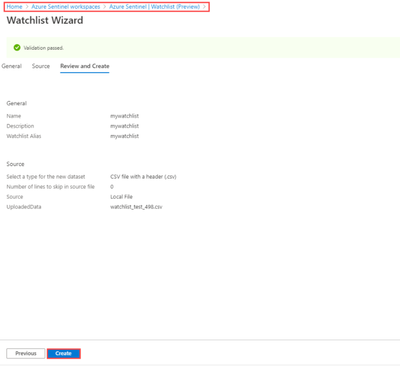
On the Source page, select the dataset type, upload a file, and then select Next.
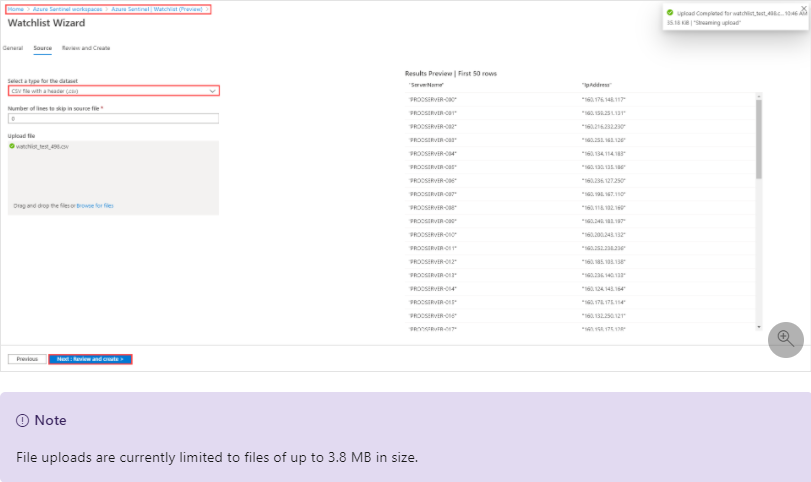
Review the information, verify that it is correct, and then select Create.
When to use Watchlists with investigations?
Watchlists can be used before, during, or after an investigation. While establishing detection rules within Azure Sentinel, Watchlists can be deployed and used within the rules if only a subset of items are required. Additionally, Watchlists can be used to serve as enrichment data for the detections. The goal for establishing a variety of Watchlists before an incident occurs is to stock up on valuable information before a compromise takes place so that the SOC team can efficiently begin an investigation the moment a compromise does happen.
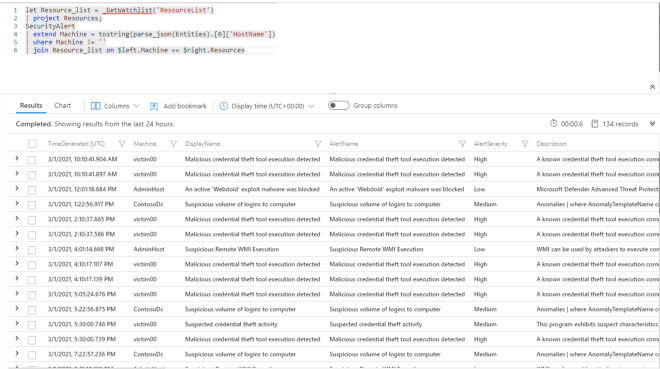
If using Watchlists during an investigation, a Watchlist can be made containing any indicators of compromise or any malicious actors that have been found during the investigation. This list can then be used to run a check on all logs within Azure Sentinel to return the logs in order to cut down on the time spent reviewing logs to find any match. The goal when using Watchlists during an investigation would be to note and compile important information that pertains to the investigation into a location to make data review more efficient.
When using Watchlists post investigation, it can house information such as machines impacted within the incident, IP’s or accounts used to carry out the attack, or external information that would have been useful to have during the investigation. Using a Watchlist after the investigation would be to ensure that if the incident or a related incident were to take place, the information would speed up the investigation and make the response more efficient.
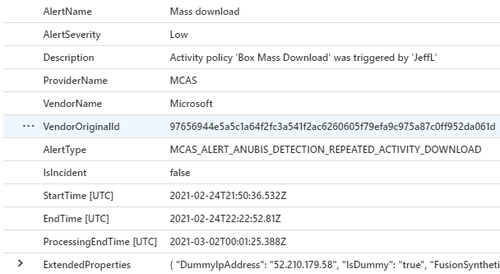
An example of using a Watchlist with manually entered enrichment information would look something like this:
This example shows how a Watchlist can add valuable information that can be used to add key details to logs, such as listing which IP ranges are associated with company sites, and which machine is associated with the IP address.
Let’s Walk Through a Scenario
A SOC team has recently set up Azure Sentinel and is in the process of expanding detection rules to cover different attack vectors. They deploy a Watchlist that contains their IP ranges for their offices that they expect to be used by users within the environment. They also set up an analytic rule that creates an incident when there is account activity that is using an IP outside of the established ranges within the Watchlist. To add to the existing Watchlist, they have also created a Playbook that will gather the IP reputation details from a source such as VirusTotal and has the Playbook pass the details into a Watchlist if it is found to be malicious.
One day, an account has been found to be compromised. The SOC team utilizes their Watchlist in a query to investigate and finds that the IP address used was outside of their IP ranges.
They utilize their Playbook in order to get the details to enrich the events they have. During the investigation, they make a note of the account compromised and create a Watchlist containing the resources that the account has access to, a list of permissions the account has, and a list of machines that the user might be using. These lists now allow the team to investigate other areas that may be impacted by the compromised account. If anything were to happen, it would allow the team to know that any incident raised regarding those resources may be related to the initial incident.
After the investigation has been done and the incident has been addressed, it was found that the account was compromised due to a greyware application that was compromised and used to gather credentials for the user. The team believes that having a list of the greyware applications that may appear on user devices will help them in the future in the event that another account is compromised. They make additional Watchlists for any additional information that they found to be useful. While wrapping up the post incident activities, they remove all Watchlists that were made during the investigation as they do not want the information from the lists to be present always in the environment.
Putting it all together
These points and examples are meant to drive discussion and thought into how Watchlists can play a factor within investigations while also achieving higher efficiency and faster response. This is one of the many features in Azure Sentinel that can be utilized in many ways, while providing immense value. Start using Watchlists while investigating incidents today!