This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
This blog post is one of the 2 posts in the tiny SQL Managed Instance series on how-to determine the status of the connectivity from inside the Azure SQL Managed Instance. They will help you to determine if the SQL MI is able to reach a certain service, such as a different SQL MI or any other supported Azure service, for example.
If you are interested in other posts on how-to discover different aspects of SQL MI - please visit the http://aka.ms/sqlmi-howto, which serves as a placeholder for the series.
When you set up a failover group between primary and secondary SQL Managed Instances in two different regions, each instance is isolated using an independent virtual network. Replication traffic needs to be allowed between these VNets.
To allow this kind of traffic, one of the prerequisites is:
- "You need to set up your Network Security Groups (NSG) such that ports 5022 and the range 11000-11999 are open inbound and outbound for connections from the subnet of the other managed instance. This is to allow replication traffic between the instances."
Strategy
We can use SQL Agent, available on SQL Managed Instance, to run some failover group related connectivity tests between both instances.
The following script will create a new job on SQL Agent named TestFoGConnection and add 2 steps, one to test port 5022 and another to test HADR port.
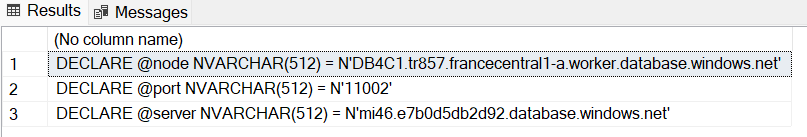
Proper values for some parameters need to be specified (@server, @node and @port), but we also have a query to generate them.
The script will trigger the job and check status every 5 seconds until it completes.
You’ll need to run the following steps twice, so you can test connectivity in both ways.
Steps
-
Connect to secondary instance.
-
Run the following script to generate parameters:
You will get something like:
Save the result to be used in next steps. Note that the parameters we just generated may change after any reconfiguration, be sure to generate them again if needed.
-
Now that we know what endpoints on secondary instance should we test against, let's connect to primary instance.
-
Paste the following script
- Replace the parameters with the values you got from step #2, like:
- Run the script and check the results, you will get something like:
Verify the results:- The outcome of each test at TcpTestSucceeded should be TcpTestSucceeded : True.
- Check if the resolved IP Address matches the range for the destination subnet, goal is to spot bad DNS resolution (like missing or wrong value).
Now, let's run the same test, but in the opposite direction
You just tested the connectivity from the primary against the secondary. We need to do the same the other way around.
Repeat the previous steps but now connect to primary to generate the parameters and then use those parameters to run the test from the secondary instance to confirm that secondary can also reach primary instance on those endpoints.
Next steps
In case there's any test failing (TcpTestSucceeded : False), this is usually a client-side networking issue (like DNS issue or a port being blocked) that you will need to pursue with your local network administrator.
We strongly recommend you request assistance from your network administrator, some validations you may do together are:
-
The Network Security Groups (NSG) on the primary managed instance subnet allows:
- Inbound access on ports 5022 and the range 11000-11999
- Outbound access on ports 5022 and the range 11000-11999
-
The Network Security Groups (NSG) on the secondary managed instance subnet allows:
- Inbound access on ports 5022 and the range 11000-11999
- Outbound access on ports 5022 and the range 11000-11999
-
The two SQL Managed Instance VNets do not have overlapping IP addresses.
-
Any networking device used (like firewalls, NVAs) do not block the traffic mentioned above.
-
Routing is properly configured, and asymmetric routing is avoided.
-
If you are using virtual network peering between different regions, ensure that global virtual network peering is supported. See more at Enabling geo-replication between managed instance virtual networks
-
If you are using peering via VPN gateway, ensure the two virtual networks are properly peered.