This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Protecting users from MFA fatigue attacks
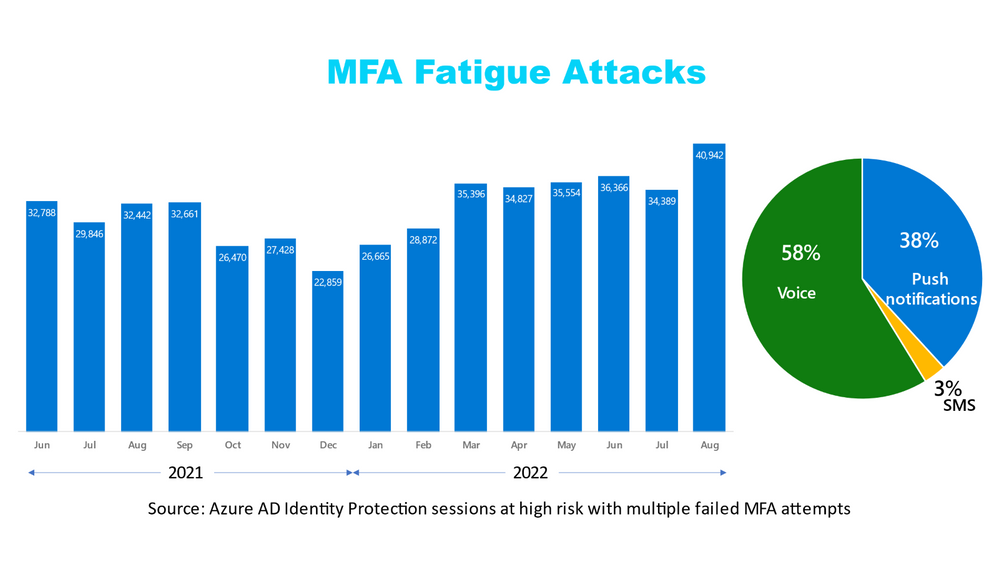
With increasing adoption of strong authentication, multi-factor authentication (MFA) fatigue attacks (aka, MFA spamming) have become more prevalent. These attacks rely on the user’s ability to approve a simple voice, SMS or push notification that doesn’t require the user to have context of the session they are authenticating. Anytime users are doing “click to approve” or “enter your PIN to approve” instead of entering a code they see on-screen, they are doing simple approvals. Our studies show that about 1% of users will accept a simple approval request on the first try. That’s why it’s critical to ensure that users must enter information from the login screen and that they have more context and protection. We track these attacks across our ecosystem, and it’s very clear they are on the rise – with push notifications, voice approvals and SMS as the top culprits.
Microsoft Authenticator is the most popular MFA method (whether after a password or in place of one) for enterprises to deploy and secure their users today. In this blog, we’ll help you protect your users on Microsoft Authenticator from MFA fatigue attacks.
We announced the protections from these attacks way back in November 2021. We’ll be enabling them for all users very soon after general availability (GA is expected in the next few months), but, given the rise in MFA fatigue attacks, we encourage you to take advantage of them now. Here’s how:
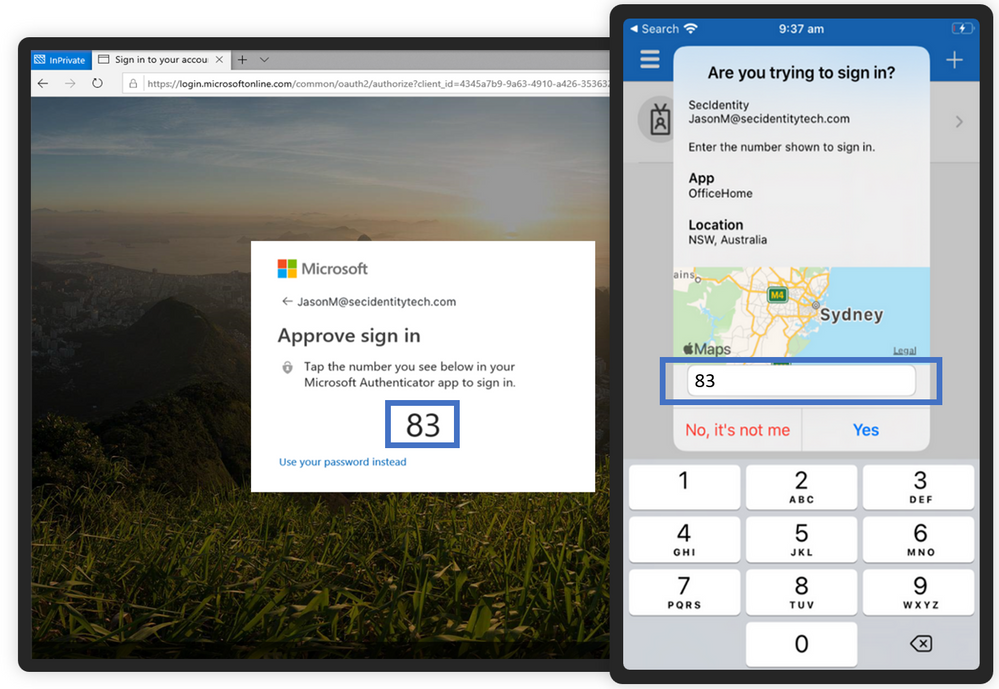
1. Prevent good users from accidentally approving sign-ins
Number matching (with "type the code" experience) prevents accidental approval by requiring the user to type in a two-digit code from the login screen to their Authenticator app. If the user didn’t initiate the sign-in, they won’t know the two-digit code, thereby requiring the bad actor to share the two-digit code in a separate channel, which the user shouldn’t accept. Number matching has been in public preview for MFA since November 2021, and almost 10K enterprises are already using it daily. It is also the default experience for passwordless phone sign-ins using Microsoft Authenticator.
Recommendation: If you haven’t yet enabled number matching for your employees, enable it today by clicking here.
Note: Number matching will be automatically enabled for all users of the Microsoft Authenticator soon after GA.
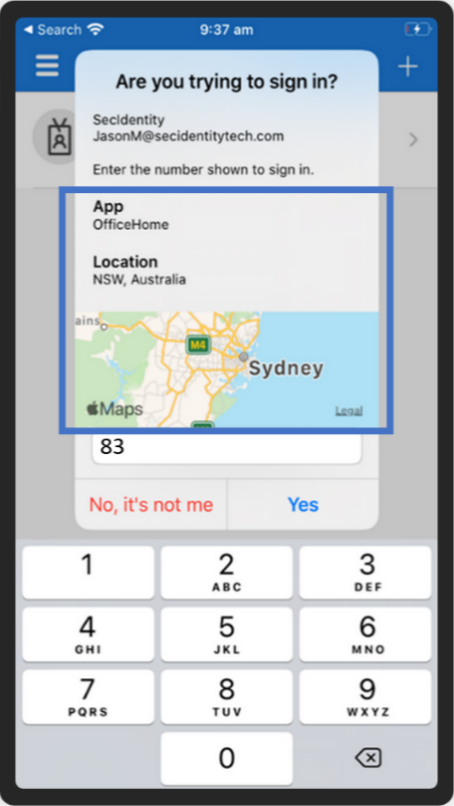
2. Help users make good decisions by providing them more context
Additional context displays additional information in the push notifications sent to your users. This includes the location (IP-based) the sign-in is coming from and the app the user is trying to access. The context helps the user understand the origin of the sign-in and thereby reduces the chances of accidental approval. Additional context has been available in public preview since November 2021 and will soon be GA for both MFA and passwordless flows.
Recommendation: If you haven’t enabled additional context for your employees yet, enable it today by clicking here.
When we performed our studies in live customer environments, number matching and additional context eliminated MFA fatigue attacks when enabled.
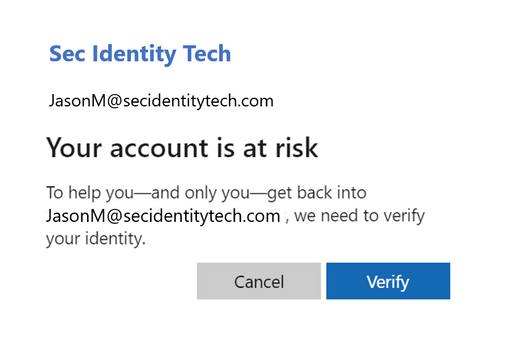
3. Still migrating to the Authenticator? Automatically change the passwords of your at-risk users
You may have users who are still migrating away from simple MFA approval mechanisms. Protect these users by automating password changes for at-risk users. If a user with simple MFA approvals enabled is getting repeated MFA requests, that means the bad actor has the user’s correct password. If a bad actor attempts a risky sign-in (e.g., from an unfamiliar location) and fails to get the approval on the MFA push notification, the user risk level is automatically elevated to the risk level of the risky sign-in. You can review at-risk users in the Azure AD Risky users report and leverage this user risk to automatically change the passwords for such users. A change of password by the user remediates the user risk and stops the bad actor from sending any more MFA requests.
Recommendation: Depending on your Azure AD licensing, you can configure risk-based Conditional Access policies to automatically prompt such users to change their password the next time they sign in.
Your security is paramount to us, and, thus, we strongly recommend that you enable these capabilities at the earliest.
One of the great things about Microsoft Authenticator is that we’re continuously investing to improve it in response to evolving attacks. We have many more enhancements on the way to protect you and ensure Authenticator remains the most secure, convenient and cost-effective authentication method for enterprises.
Best regards,
Alex Weinert (@Alex_T_Weinert)
Director of Identity Security
Microsoft Identity and Network Access Security Team
Learn more about Microsoft identity:
- Return to the Azure Active Directory Identity blog home
- Join the conversation on Twitter and LinkedIn
- Share product suggestions on the Azure Feedback Forum