This post has been republished via RSS; it originally appeared at: Microsoft Tech Community - Latest Blogs - .
Service Fabric Explorer (SFX) is the web client used when accessing a Service Fabric (SF) cluster from a web browser. The version of SFX used is determined by the version of your SF cluster. We are providing this update to make customers aware that switching from the default web client to use the older SFX web client could increase their risk when an attacker has already gained access to a privileged account.
Affected versions Prior to SF runtime version 8.1.316, the vulnerable version of SFX (SFXv1) was the default client in the SF runtime. From SF version 8.1.316 onward, the default SFX client is SFXv2, which is not vulnerable to this attack.
· SFXv1 is shipped in current versions of the product, but SFXv2 is the default client.
· For SF versions starting with 8.2.1235, SFXv1 is accessible through the advanced options menu. An upcoming release of SF will remove SFXv1 and the option to switch to it.
· From SF versions from 8.1.316 (inclusive) and prior to 8.2.1235, SFXv1 is accessible by choosing the “Leave Beta” option on the home page.
· Out of support versions of Service Fabric may have SFXv1 as the default client.
Potential Attack Vector
An attacker that has acquired management privileges in the cluster can deploy and persist scripts in the cluster which may then be executed in the SFX session of another user connected to the same cluster. The script may be any valid HTML or JavaScript code, embedded as text in some of the elements rendered in SFX, such as service settings, or events raised by a service.
How to tell if you are accessing the older, vulnerable version
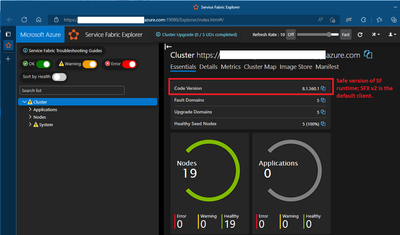
Figure 1 below depicts the default landing page for the non-vulnerable default web client version of the Service Fabric cluster (SFXv2).
Figure 1: Default non-vulnerable web client SFXv2
There are two ways customers could be accessing the old vulnerable SFXv1:
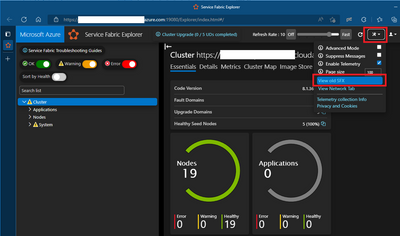
- Customers using the default safe web client (SFXv2) have the ability to select View old SFX from the advanced menu dropdown (see Figure 2 below). We recommend customers stop taking this action and use the default safe web client to remain secure.
Figure 2: The vulnerable SFXv1 is accessible via dropdown in the current default safe web client SFXv2
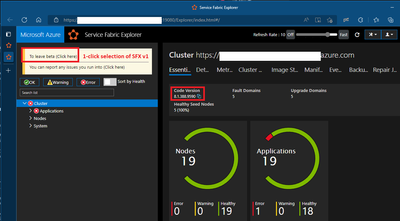
- For customers using older SF versions, the vulnerable SFXv1 can be selected by clicking To leave beta (Click here) as shown in Figure 3 below. Note that “beta” refers to the default SFXv2 web client. The term is not indicative of the quality or support level of SFX v2.
. We recommend customers upgrade to the latest SF version and discontinue use of any older versions.
Figure 3: Older SF versions have one-click SFXv1 access
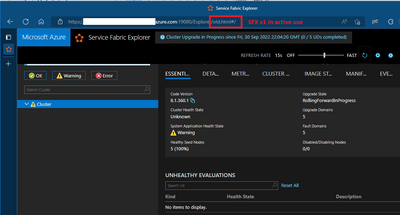
To verify whether you are using SFXv1, examine the SFX URL. If /old.html appears in the URL, you are using the vulnerable version. See Figure 4 below.
Figure 4. Confirming/detecting that SFX v1 is active/in effect.
Mitigations
Again, we recommend all Service Fabric customers upgrade to a supported Service Fabric runtime version and refrain from accessing the vulnerable SFXv1.
We thank Orca Security for informing us of this vulnerability and working with us under Coordinated Vulnerability Disclosure to help protect our customers.