This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Community Hub.
Microsoft Defender External Attack Surface Management (EASM) continuously discovers a large amount of up-to-the-minute attack surface data, helping organizations know where their internet-facing assets lie. Connecting and automating this data flow to all our customers’ mission-critical systems that keep their organizations secure is essential to understanding the data holistically and gaining new insights, so organizations can make informed, data-driven decisions.
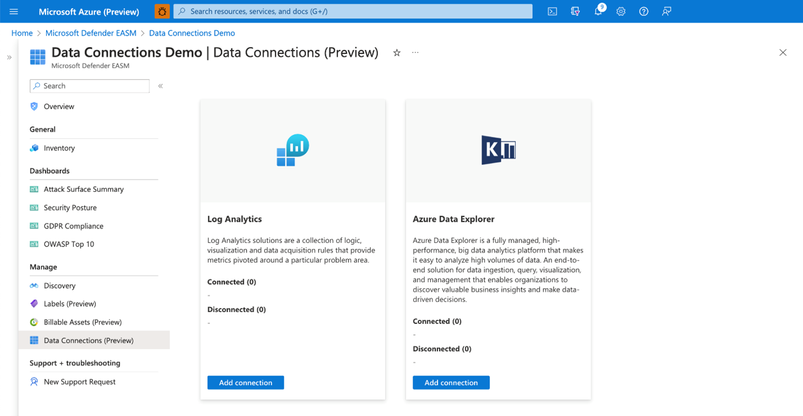
In June, we released the new Data Connections feature within Defender EASM, which enables seamless integration into Azure Log Analytics and Azure Data Explorer, helping users supplement existing workflows to gain new insights as the data flows from Defender EASM into the other tools. The new capability is currently available in public preview for Defender EASM customers.
Why use data connections?
The data connectors for Log Analytics and Azure Data Explorer can easily augment existing workflows by automating recurring exports of all asset inventory data and the set of potential security issues flagged as insights to specified destinations to keep other tools continually updated with the latest findings from Defender EASM. Benefits of this feature include:
- Users have the option to build custom dashboards and queries to enhance security intelligence. This allows for easy visualization of attack surface data, to then go and perform data analysis.
- Custom reporting enables users to leverage tools such as Power BI. Defender EASM data connections will allow the creation of custom reports that can be sent to CISOs and highlight security focus areas.
- Data connections enable users to easily access their environment for policy compliance.
- Defender EASM’s data connectors significantly enrich existing data to be better utilized for threat hunting and incident handling.
- Data connectors for Log Analytics and Azure Data Explorer enable organizations to integrate Defender EASM workflows into the local systems for improved monitoring, alerting, and remediation.
In what situations could the data connections be used?
While there are many reasons to enable data connections, below are a few common use cases and scenarios you may find useful.
- The feature allows users to push asset data or insights to Log Analytics to create alerts based on custom asset or insight data queries. For example, a query that returns new High Severity vulnerability records detected on Approved inventory can be used to trigger an email alert, giving details and remediation steps to the appropriate stakeholders. The ingested logs and Alerts generated by Log Analytics can also be visualized within tools like Workbooks or Microsoft Sentinel.
- Users can push asset data or insights to Azure Data Explorer/Kusto to generate custom reports or dashboards via Workbooks or Power BI. For example, a custom-developed dashboard that shows all of a customer’s approved Hosts with recent/current expired SSL Certificates that can be used for directing and assigning the appropriate stakeholders in your organization for remediation.
- Users can include asset data or insights in a data lake or other automated workflows. For example, generating trends on new asset creation and attack surface composition or discovering unknown cloud assets that return 200 response codes.
How do I get started with Data Connections?
We invite all Microsoft Defender EASM users to participate in using the data connections to Log Analytics and/or Azure Data Explorer so you can experience the enhanced value it can bring to your data, and thus, your security insights.
Step 1) Ensure your organization meets the preview prerequisites
|
Aspect |
Details |
|
Required/Preferred Environmental Requirements |
Defender EASM resource must be created and contain an Attack Surface footprint. |
|
Required Roles & Permissions |
- Must have a tenant with Defender EASM created (or be willing to create one). This provisions the EASM API service principal. - User and Ingestor roles assigned to EASM API (Azure Data Explorer) |
Step 2) Access the Data Connections
Users can access Data Connections from the Manage section of the left-hand navigation pane (shown below) within their Defender EASM resource blade. This page displays the data connectors for both Log Analytics and Azure Data Explorer, listing any current connections and providing the option to add, edit or remove connections.
Connection prerequisites: To successfully create a data connection, users must first ensure that they have completed the required steps to grant Defender EASM permission for the tool of their choice. This process enables the application to ingest our exported data and provides the authentication credentials needed to configure the connection.
Step 3: Configure Permissions for Log Analytics and/or Azure Data Explorer
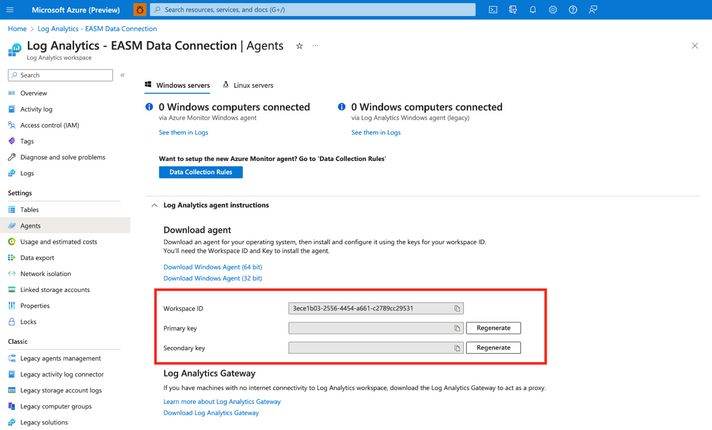
Log Analytics:
- Open the Log Analytics workspace that will ingest your Defender EASM data or create a new workspace.
- On the leftmost pane, under Settings, select Agents.
Azure Data Explorer:
- Expand the Log Analytics agent instructions section to view your workspace ID and primary key. These values are used to set up your data connection.
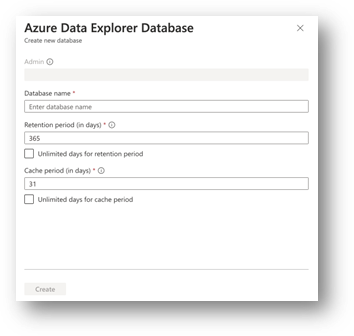
- Open the Azure Data Explorer cluster that will ingest your Defender EASM data or create a new cluster.
- Select Databases in the Data section of the left-hand navigation menu.
Select + Add Database to create a database to house your Defender EASM data.
4. Name your database, configure retention and cache periods, then select Create.
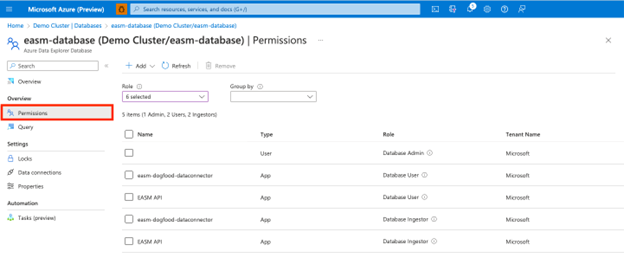
5. Once your Defender EASM database has been created, click on the database name to open the details page. Select Permissions from the Overview section of the left-hand navigation menu.
To successfully export Defender EASM data to Data Explorer, users must create two new permissions for the EASM API: user and ingestor.
6. First, select + Add and create a user. Search for “EASM API,” select the value, then click Select.
7. Select + Add to create an ingestor. Follow the same steps outlined above to add the EASM API as an ingestor.
8. Your database is now ready to connect to Defender EASM.
Step 4: Add data connections for Log Analytics and/or Azure Data Explorer
Log Analytics:
Users can connect their Defender EASM data to either Log Analytics or Azure Data Explorer. To do so, select “Add connection” from the Data Connections page for the appropriate tool. The Log Analytics connection addition is covered below.
A configuration pane will open on the right-hand side of the Data Connections screen as shown below. The following fields are required:
- Name: enter a name for this data connection.
- Workspace ID For Log Analytics, users enter the Workspace ID and the coinciding API key associated with their account.
- Api key Log Analytics users enter the API key associated with their account
- Content: users can select to integrate asset data, attack surface insights, or both datasets.
- Frequency: select the frequency that the Defender EASM connection sends updated data to the tool of your choice. Available options are daily, weekly, and monthly.
Azure Data Explorer:
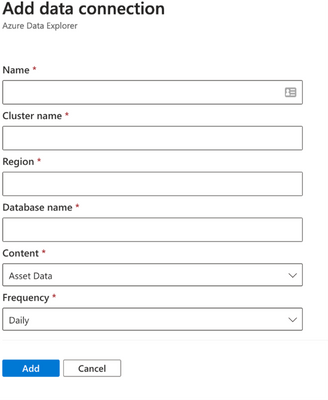
The Azure Data Explorer connection addition is covered below.
A configuration pane will open on the right-hand side of the Data Connections screen as shown below. The following fields are required:
- Name: enter a name for this data connection.
- Cluster name:
- Region: The region associated with Azure Data explorer
- Database: The database associated with the Azure Data explorer
- Content: users can select to integrate asset data, attack surface insights, or both datasets.
- Frequency: select the frequency that the Defender EASM connection sends updated data to the tool of your choice. Available options are daily, weekly, and monthly.
Step 5: View data and gain security insights
To view the ingested Defender EASM asset and attack surface insight data, you can use the query editor available by selecting the ”Logs” option from the left hand menu of the Azure Log Analytics Workspace you created earlier. These tables are also updated at the Data Connection configuration record frequency.
Extending Defender EASM Asset and Insights data, via these two new data connectors, into Azure ecosystem tools like Log Analytics and Data Explorer enables customers to orchestrate the creation of contextualized data views that can be operationalized into existing workflows and provides the facility and toolsets for analysts to investigate and develop new methods of applicative Attack Surface Management.
Additional resources: