This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
The Office cloud policy service (OCPS) is a cloud-based service that enables you to apply policy settings for Office 365 ProPlus on a user’s device. The policy settings roam to whichever device the user signs into and uses Office 365 ProPlus. As end users become increasingly mobile, IT Pros need a single approach to secure Office 365 ProPlus for traditional on-premises domain devices, Azure AD registered devices, Azure AD Joined, and Hybrid Azure AD joined devices. OCPS applies to all scenarios above without the need to download and replicate any content such as Administrative Template files (ADMX/ADML) on-premises. The goal of this blog is to provide some transparency of how the service works to help IT Pros during their validation phase and to encourage transition from classic domain-based policy to OCPS service for Office 365 ProPlus.
Requirements of OCPS
1. At least Version 1808 (August 2018) of Office 365 ProPlus
2. User accounts created in or synchronized to Azure Active Directory (AAD). The user must be signed into Office 365 ProPlus with an AAD based account.
3. Security groups created in or synchronized to Azure Active Directory (AAD), with the appropriate users added to those groups.
4. To create a policy configuration, you must be assigned one of the following roles in Azure Active Directory (AAD): Global Administrator, Security Administrator, or Office Apps Admin.
5. Connectivity to addresses below. Microsoft recommends proxy bypass\whitelist for these URLs
*.manage.microsoft.com, *.officeconfig.msocdn.com, config.office.com over 443
Steps to perform proof of concept and validation
1. Create a test user, ours will be “Gottlieb Daimler”, gdaimler@contoso.com.
2. Create security group “OCPS Service Validation” and add user to group within Active Directory Users and Computers.
3. Allow AAD Connect to synchronize user and group to Azure AD. (lunch break :) or force synchronization via commands below)
(optional) From AAD Connect Server and elevated PowerShell, run the following commands:
PS C:\WINDOWS\system32>import-module adsync
PS C:\WINDOWS\system32>Set-ADSyncScheduler -NextSyncCyclePolicyType Delta
PS C:\WINDOWS\system32>Start-ADSyncSyncCycle
Browse Azure AD portal and explore Users – All Users, select Gottlieb Daimler and then Groups. Verify that group “OCPS Service Validation” has been assigned and source says, “Windows Server AD”. This confirms user and group were synced into Azure AD successfully and we can proceed to next steps.
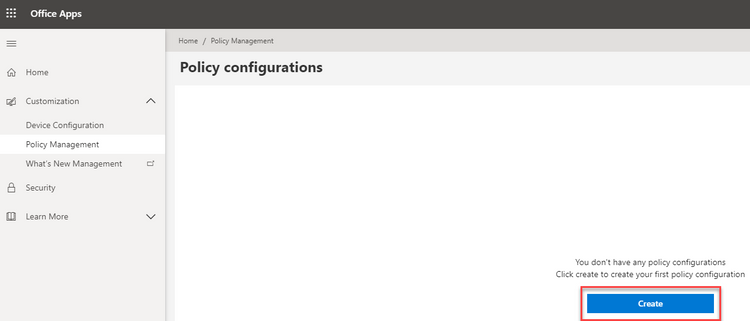
4. Create your first OCPS policy and select “Create” button:
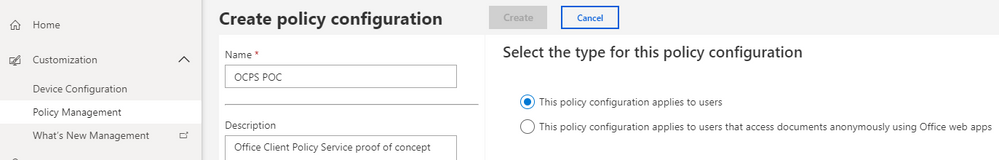
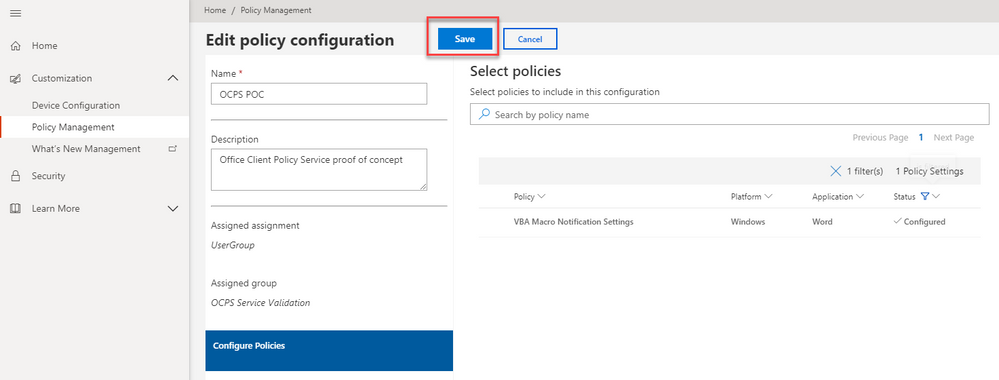
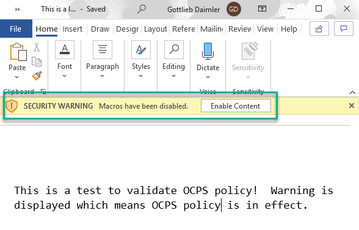
5. Complete input fields, when selecting assigned security group input “OCPS” and service should filter results to “OCPS Service Validation” group. Next, define a policy. For the demo, I chose policy "VBA Macro Notification Settings", "Enabled" where VBA Macro Notification Settings are set to "Disable all with notification". Once selections have been made “Create” or “Save”.
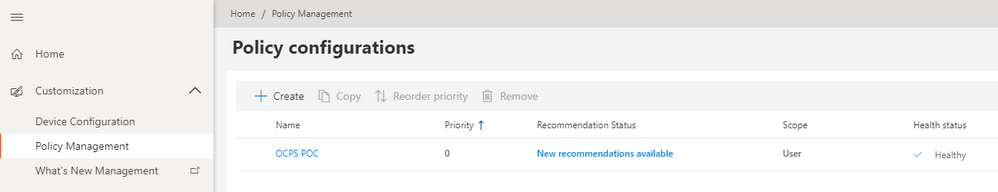
6. From Policy Management, we can now see our policy exists.
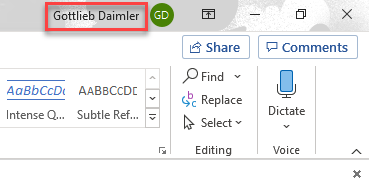
So, we’ve got a policy, we’ve assigned it to a security group containing our test user, our next step is to validate. My test machine happens to be classic on-premises domain joined machine. My user, Gottlieb Daimler, is signed in with his normal Active Directory credentials which is displayed in upper right hand corner of Word.
Traditional Group Policy uses Client-Side Extensions in Windows to apply policy every 90 minutes. IT Pros can force policy by using command line “gpupdate /force” and inspect\verify registry as well as application behavior prior to broad deployment. OCPS checks for policy upon initial Office application launch, calls into cloud service endpoints listed above, determines policy applicability based on group membership and priority assignment and registry keys are populated.
Specifically, there are two locations of interest in registry.
1. HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\CloudPolicy\
This will contain information about FetchInterval, 90 minutes is default, as well as record of Last Fetch Time and Last Payload Hash.
2. HKEY_CURRENT_USER\Software\Policies\Microsoft\Cloud. This key will contain path to registry keys representing the policy assignment. For example, ours will be HKEY_CURRENT_USER\Software\Policies\Microsoft\Cloud\Office\16.0\word\security
Vbawarnings = 2 (DWORD)
IT Pros can achieve the same behavior of gpupdate by simply deleting the key HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\CloudPolicy, close Office application and relaunch to fetch policy. I typically use tools like Process Monitor to help trust\verify operations of this type with filters such as “Path” contains “CloudPolicy” or where Operation is “RegSetValue” etc. Opening a Word document containing a Macro displaying warning with notification as expected.
FAQ:
How does conflict resolution work if the same policy is set via traditional domain-based policy as well as OCPS?
OCPS takes priority if there are any conflicts with traditional domain-based policies.
Currently policies are limited to user settings. Are there plans on adding machine settings?
Yes. This has been accepted and currently is in our backlog. We hope to have this available next year.
Group Policy provides a view of all policies on the device or for the specified user. Does OCPS support this?
Currently OCPS does not provide a list of all Office policies applied to a specific user or device. This is on our backlog and we hope to have this available next year.
Will OCPS support other platforms such as MacOS, Android and iOS?
Yes, OCPS in the future will also support additional platforms such as MacOS, Android and iOS. We will create additional blog postings per platform once features are generally available.
Are there any environments where OCPS is not available?
The Office cloud policy service isn't available to customers who have the following plans: Office 365 operated by 21Vianet, Office 365 Germany, Office 365 GCC, or Office 365 GCC High and DoD.
The Author
This blog post is brought to you by Dave Guenthner, a Senior Premier Field Engineer and “ProPlus Ranger” at Microsoft. Feel free to share your questions and feedback in the comments below.