Proactive Threat Hunting
As security analysts and investigators, you want to be proactive about looking for security threats, but your systems and security appliances generate mountains of data that can be difficult to parse and filter into meaningful events. This is where hunting with Azure Sentinel can help.
Hunting Dashboard Refresh
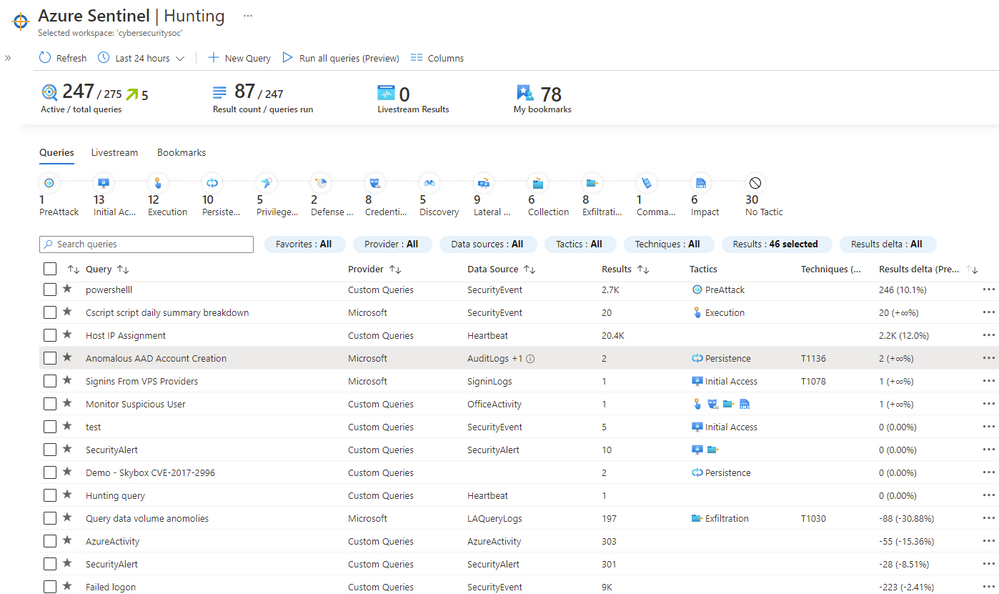
Now in preview, we refreshed the hunting query experience to help you find undetected threats in your environment more quickly. We also provide new ways to identify which hunting results are most relevant to your environment and your desired attack scenarios.
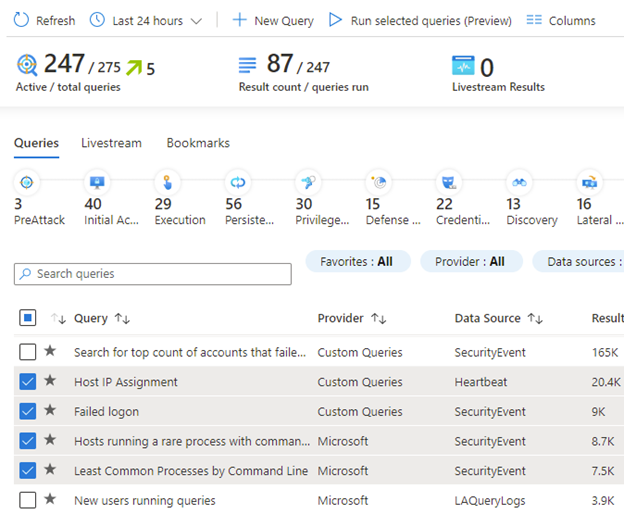
You can now run all your hunting queries, or a selected subset, in a single click. You can look at the “Result count / queries run” metric counts to see your progress. This can be very helpful when running many queries across large data sets.
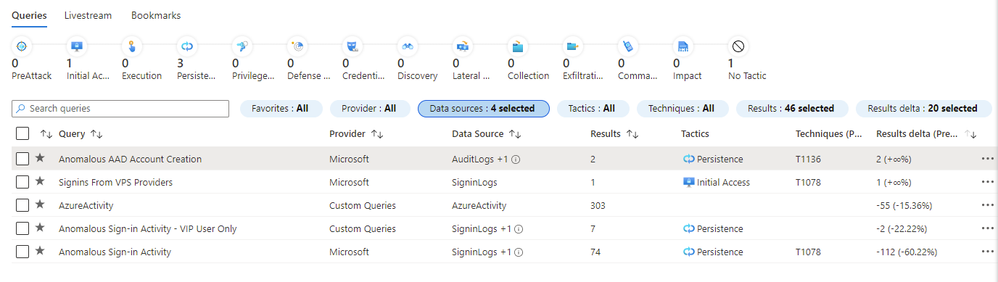
To get a fine-grained view of which results to examine, you can search for or filter results based on specific MITRE ATT&CK Techniques. You can also see which results have changed the most in the last 24 hours using the new “results deltas” field to identify spikes of activity.
As you narrow down which query and results you want to look at, the new MITRE ATT&CK tactic bar totals update to show which MITRE ATT&CK tactics apply. This is an easy way to see which tactics show up when you filter by a given result count, high result delta, or any other set of filters.
We are always adding more hunting content. So be sure to check out our Github repository to see the latest hunting queries. We will appreciate your feedback and look forward to growing our hunting community together.
Further Reading
- Hunting capabilities in Azure Sentinel: https://docs.microsoft.com/en-us/azure/sentinel/hunting
- Azure Sentinel Hunting Queries on Github: https://github.com/Azure/Azure-Sentinel/tree/master/Hunting%20Queries