This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Protecting IoT devices using a Zero Trust approach is a security imperative
Even in the face of significant security challenges organizations continue to rapidly adopt Internet of Things (IoT). They understand IoT adoption is critical to their digital transformation journey and to advancing their business’s interests. This trend is not limited so a single industry and is in fact It’s happening across all industries including automotive, financial, healthcare, retail, energy, agriculture just to name a few.
The scenarios for IoT devices are incredibly diverse ranging from highly sophisticated autonomous vehicles and medical devices that capturing real time data to the most simple sensors such as those that monitor the occupancy of a parking space at a local shopping center. Theis diversity in these scenarios leads to diversity in the devices themselves at the hardware, operating system and application level and also in terms of form factor. Many devices are quite small,and consume littlesmall amounts of power and must be low costs and because of this don’t have the computing power to integrate sophisticated firewalls, antivirus and other security capabilities to protect them. The security challenges are further complicated by the diverse environments these devices are deployed within - ranging from inside factories with physical security measures in place to help protect them to remote locations and public spaces where physical access to device is literally there for anyone which malicious intent to tamper with. IoT devices are exposed in unique ways and offer high-value targets to attackers. Sometimes the IoT devices themselves are of interest to attackers but often times these devices are used as means to gain access to the network they are connected to which may have more interesting targets to attack. All of these factors make securing IoT devices an absolute imperative.
A large majority of our of our customers are familiar with some of these challenges. In fact a recent study conducted by Microsoft found that 97% of security decision makers believe IoT related security is a key concern and they are actively looking for better solutions and approaches securing them. Many of these same organizations are turning to a Zero Trust security approach to address these concerns.
How to implement zero trust in my IoT organization?
Today, there few if any security professionals that are unaware of Zero Trust, nearly every CIO, CTO, or CISO understands the benefits and is now on the journey to learn more about implementation best practices and that solution that can help. Microsoft recently published a Zero Trust for IoT best practice and maturity model that organizations can use to design their own Zero trust roll-out strategy based on their unique business needs. The model principal assumes you must verify any connection in your network before you trust it and then explicitly verify the security status of each identity, endpoint, network, and other resources based on all available signals and data.
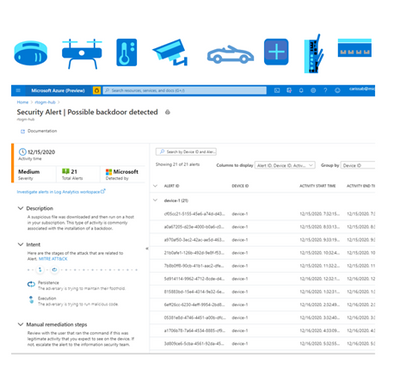
How can Azure Defender for IoT help you achieve Zero Trust?
The Azure Defender for IoT provides both agentless and agent based options to help achieve Zero Trust and today we’re are going to focus on the agent based option. With it a Zero Trust model and security controls can be implemented across each of the Zero Trust pillars which identities, network, data and .
Defender for IoT offers a lightweight security “micro” agent that can be embedded into IoT device, supporting any major IoT Operating system . This agent gives Defender for IoT a much richer set of signals to monitor than can be achieved by using network signals alone. For instance, because agents can monitor the identities, processes, data being used on the device itself our ability to detect malicious and anomalous behaviors is significantly enhanced. With it we have a much better understanding of what is happening, and we can rely a lot less on inference which can lead to false alerts. The agent performs little processing and forwards event data from the device to the Azure Defender for IoT cloud services, for ongoing monitoring of your network, assisting to enforce device compliance to a secure access which helps to prevent attackers from moving laterally across the network
With the ability to perform and compliance assessments on agent based IoT devices Defender for IoT provides you with strong Zero Trust controls. It monitors for invalid configurations and operating system updates on your devices and assesses them against vulnerability assessment standards like those from the Center for Internet Security (CIS). Additionally, Defender for IoT applies behavioral analytics to both device and network telemetry to monitor and quickly detect anomalies and unauthorized activities. For instance, scenarios like:
- Is the device communicating outside of the normal hours?
- Is the device performing unauthorized outbound connections?
and many more can be achieved enabling you to indicate about a potential attack threats running on the device and ultimately take protective actions to improve your IoT security posture.
Azure Defender for IoT can also integrate with Azure Sentinel and even 3rd party SIEM systems giving security operations more comprehensive forensic capabilities and anomaly remediation for a better Zero Trust maturity and control.
We hope you find this information helpful, and we would love to hear from you. join us out community :
Azure Defender for IoT - Microsoft Tech Community
For more information about Azure Defender for IoT check out the following resources:
Azure Defender for IoT | Microsoft Azure Defender for IoT
What is agent-based solution architecture
If you have any suggestions, questions, or comments, please visit us on our discussion form on Microsoft Tech Community