This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
This post is written together with
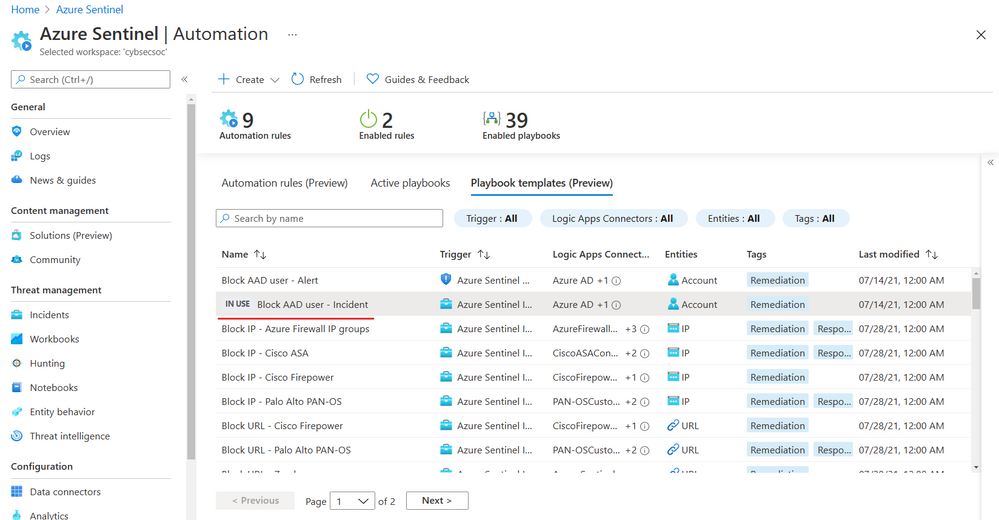
Today, we are announcing the Public Preview of the Playbook Templates Tab, which you can find under the Automation menu, as a new feature in the Microsoft Sentinel.
This feature is released as part of Microsoft Sentinel SOAR out-of-the-box content announcement, exposing the leading scenarios in-product while making it easier to start using playbooks.
Microsoft Sentinel provides many out-of-the-box contents to customers - either in the feature galleries (like Analytics rule templates, Workbook templates, Notebooks, and now Playbooks) or from the Microsoft Sentinel GitHub repository.
A playbook template is a pre-built, tested, and ready-to-use workflow that you can customize to meet your needs. Templates can also serve as a reference for best practices when developing playbooks from scratch or inspiration for new automation scenarios. Playbook templates are not active playbooks until you create a playbook from the template.
The playbook templates are based on common automation scenarios that our customers use in their SOCs. Many of these playbooks are contributed by the Microsoft security professionals and Microsoft Sentinel community, and are originally located in the Microsoft Sentinel GitHub repository.
If the playbook template is deployed, an IN USE tag will appear next to the playbook name. If you re-deploy the template with the same name, the original playbook will be overwritten.
If the playbook template is deployed and there is an update available, an UPDATE AVAILABLE tag will appear next to the playbook name, and you will be able to update the playbook by clicking on the update tag.
Additional automations experience improvements
New deployment wizard for templates
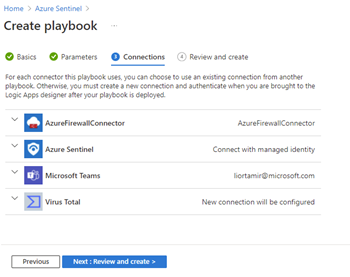
New templates experience also includes a new deployment wizard, which allows smooth creation of an active playbook from a selected template. Wizard allows customers to enter parameters that make playbook specific for their usage. Also, you can select previously used API connections, and the Microsoft Sentinel connector is deployed by default with managed identity auth type.
After following the wizard steps, you are taken to the created playbook’s Logic Apps designer, where you can customize the playbook or complete any post-deployment steps. From here, you can quickly pivot back to the Microsoft Sentinel experience. This approach is a significant improvement compared to the deployment from the GitHub experience.
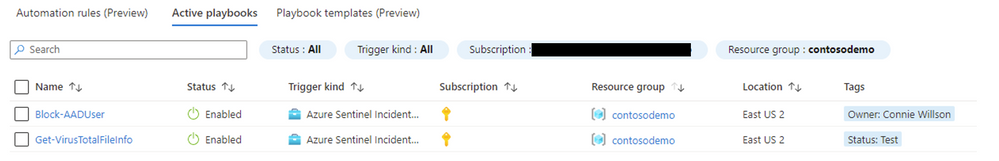
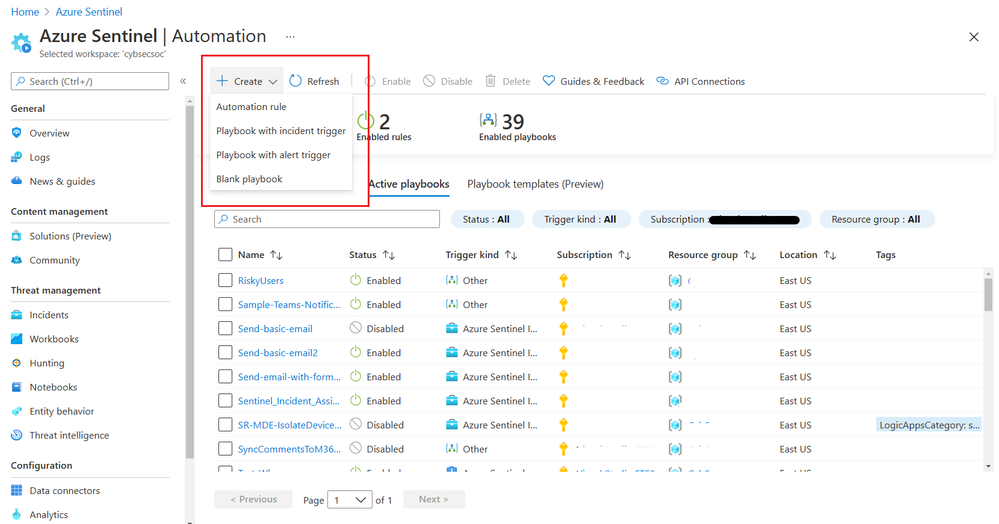
Active Playbooks tab improvements
After creating a playbook from the template (or from scratch), you can manage playbooks from the Active Playbooks tab (formally known as “Playbooks”). Also, new columns and filters for Resource Group and a new column for Tags are added based on customer requests.
Create playbooks from scratch faster
Previously, to create a Sentinel playbook that leverages the Microsoft Sentinel trigger, you would have to go through the general Logic Apps creation process, choose a blank template, and look for Microsoft Sentinel triggers. Now you can directly create a playbook that starts with the incident or alert trigger.
Use-Cases & Scenarios Available in Playbook Templates Tab
Playbooks in the templates tab are tagged by their scenario. Let’s take some examples:
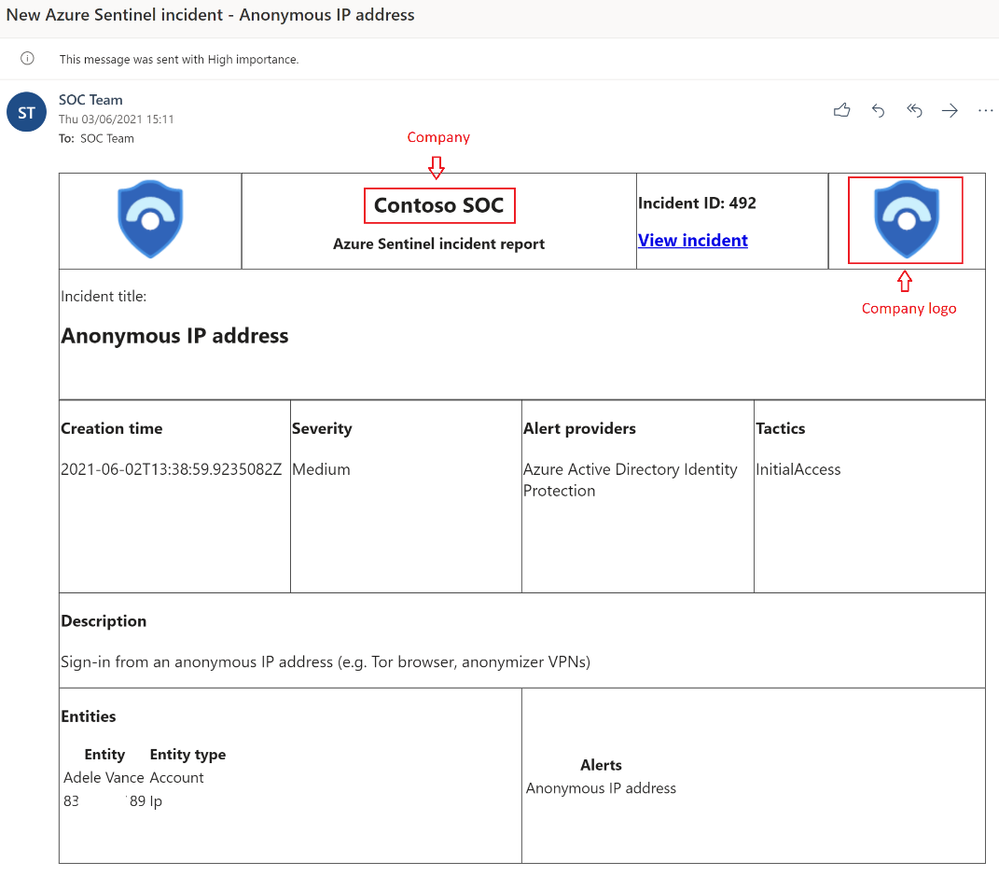
- Notification: Send e-mail with formatted incident report
This playbook picks up details from an incident such as alerts, entities, description, creation date, URL to the incident. Then it sends those details formatted to a specific e-mail address when a Microsoft Sentinel incident is created. An analyst can quickly check severity, what tactics and entities are associated with the incident, and use the incident link to guide analysts directly to the specific incident page in the Microsoft Sentinel.
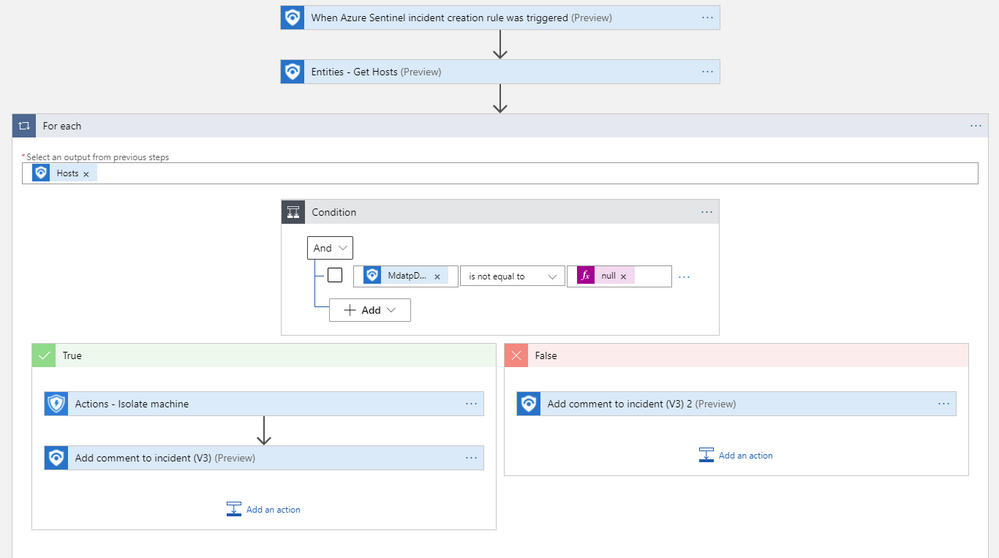
- Remediation: Isolate endpoint – MDE
This playbook will get the hosts from the incident and, using Microsoft Defender for Endpoint Logic App connector, isolate that specific device if available in MDE. Based on the result (isolated or not), a comment will be added to the incident so that SOC analysts can have easy access to information. This is another example of how SOC analysts can use Microsoft Sentinel playbooks to act in a matter of seconds, without leaving the environment, and maybe even stopping the spread of threat through the rest of the network. - Sync: Create SNOW record
A typical use case will be to synchronize incident details with the ticketing systems. ‘Create SNOW record’ playbook extracts data from an incident like title, description, URL, severity and creates SNOW records based on severity level. SOC analysts can easily access essential information about incidents created and links that will guide them to the specific incident page from the ticketing system.
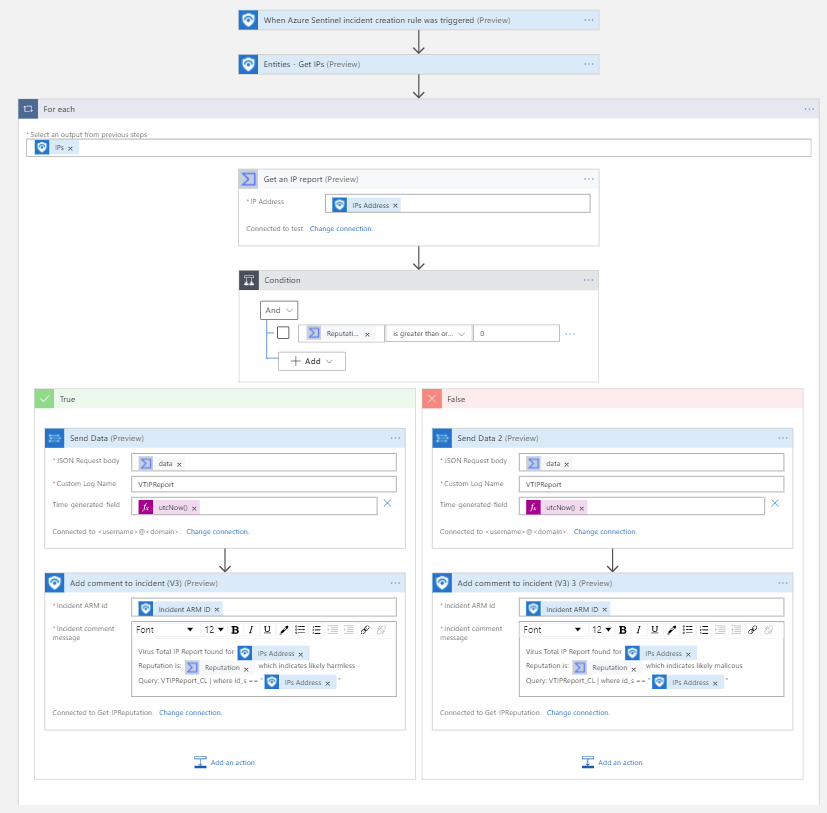
- Enrichment: IP Enrichment - Virus Total report
Enrichment playbooks are used to enrich incidents with more data to enable SOC analysts to improve Mean Time to Respond/Remediate (MTTR). ‘IP Enrichment - Virus Total report’ queries IP against Virus Total and, based on results, adds info to the Virus Total custom table (VTIPReport_CL) and adds a comment to the incident. The playbook can run as soon as an incident is created by assigning the playbook to the automation rule. With this, as soon as SOC analysts open’s incident page, information about IP reputation will be available in the comment, thus expediting time to resolve an incident.
- Utilities and Incident management playbooks
As the volume of the security data is incising, there is a need to help organizations orchestrate the SOC's operation. Let's use the 'Incident Assignment Shifts' playbook as an example: this playbook will assign incidents to your analysts based on their Microsoft Teams shifts while balancing the capacity of each team member.
To learn how to create and customize Microsoft Sentinel playbooks from built-in templates, please visit the official Microsoft docs – link.
We hope you found this article useful. Please leave us your feedback and questions in the comments section.
Thanks to the Microsoft Sentinel CxE team for reviewing the content.
Learn more