This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
Today, we are excited to announce the preview of a core set of our industry leading prevention and protection capabilities for client endpoints running Windows, macOS, Android, and iOS. This new solution will make it easier for more security teams across the globe to buy and adopt the best of breed fundamentals of Microsoft Defender for Endpoint.
The threat landscape is more complex than ever. Organizations with already limited resources are trying to keep up, while also ensuring that they have a Zero Trust security strategy that evolves with ever changing threats and their own organizational needs.
The endpoint remains one of the most targeted attack surfaces as new and sophisticated malware and ransomware continue to be prevalent threats. As we move into the second half of 2021, ransomware in particular continues to persist and evolve, financial damage continues to increase, and the impact is felt across numerous industries - not just in private sector but also across public infrastructures.
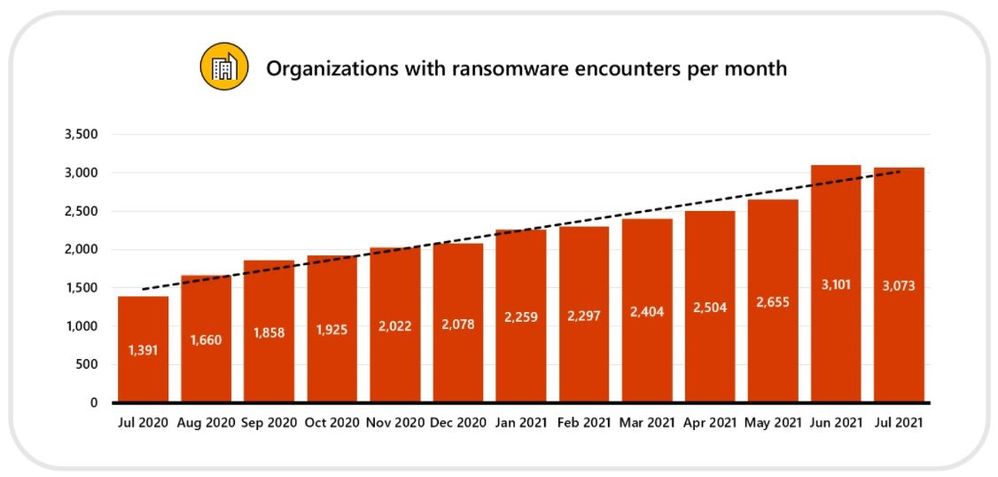
Over the last year, Microsoft security researchers have tracked nearly a 121% increase in organizations who have encountered ransomware (July 2020 - July 2021) as shown in the chart below.
The level of sophistication of these kinds of attacks and the speed at which they evolve requires a different approach to security, one that is based on cloud native technology, built on deep threat and human intelligence, and that can easily scale. It requires robust prevention that uses AI and machine learning to rapidly stop threats and a solution that enables a Zero Trust approach.
Delivering security for all
Microsoft is committed to delivering best of breed, multi-platform, and multi-cloud security for all organizations across the globe. Our aim is to offer simplified, comprehensive protection that prevents breaches and enables our customers to innovate and grow. As part of that commitment, we’re excited to offer a foundational set of our market leading endpoint security capabilities for Windows, macOS, Android, and iOS at a lower price in a new solution to be named Microsoft Defender for Endpoint Plan 1 (P1).
With Microsoft Defender for Endpoint P1, customers will get the following core capabilities:
- Industry leading antimalware that is cloud-based with built-in AI that helps to stop ransomware, known and unknown malware, and other threats in their tracks.
- Attack surface reduction capabilities that harden the device, prevent zero days, and offer granular control over access and behaviors on the endpoint.
- Device based conditional access that offers an additional layer of data protection and breach prevention and enables a Zero Trust approach.
All of these capabilities stand on the same strong foundation that all Microsoft Defender for Endpoint customers benefit from today:
- Cloud powered solution with nearly infinite scale to meet your needs – no additional IT costs, no compatibility issues, no waiting for updates.
- Unparalleled breadth and depth of built-in threat and human intelligence powered by machine learning models and AI.
- A unified solution offering unmatched threat visibility, incident correlation and insight, and a world class SecOps experience as part of Microsoft 365 Defender – our XDR solution.
Microsoft Defender for Endpoint P1 delivers on our endpoint security promise to help organizations rapidly stop attacks, scale their security resources, and evolve their defenses and is available in preview today. Our existing endpoint security solution will continue to be offered without changes and named Microsoft Defender for Endpoint Plan 2 (P2).
Comparing solutions
The new Plan 1 is a subset of the capabilities that are in Microsoft Defender for Endpoint today - as highlighted in green in our capability graphic below. It offers organizations the foundational security they need against malware, and other threats such as ransomware, and helps organizations get started on their Zero Trust journey with capabilities that control access and behaviors on the endpoint as well as enable conditional access.
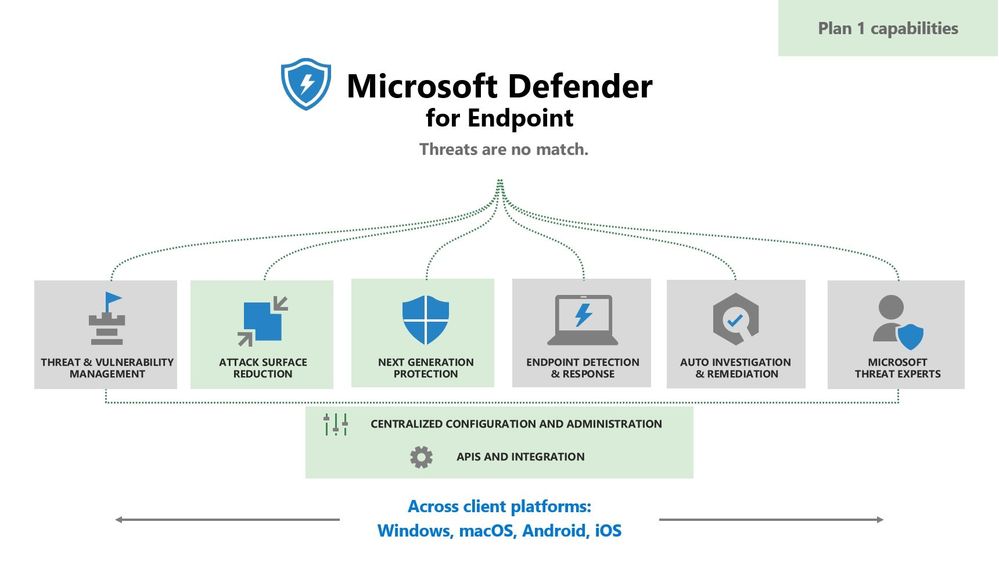
Customers that seek Plan 1 are those that are looking for EPP (endpoint protection) capabilities only. Plan 1 offers best of breed fundamentals in prevention and protection for client endpoints running Windows, macOS, Android, and iOS. It includes next generation protection, device control, endpoint firewall, network protection, web content filtering, attack surface reduction rules, controlled folder access, device based conditional access, APIs and connectors, and the ability to bring your own custom TI. Finally, it includes access to the Microsoft 365 Defender security experience to view alerts and incidents, security dashboards, device inventory, and perform investigations and manual response actions on next generation protection events.
For the most complete endpoint security solution, Plan 2 is by far the best fit for enterprises that need a solution with advanced threat prevention and detection, deep investigation and hunting capabilities, and advanced SecOps investigation and remediation tools. Plan 2 capabilities further prevent security breaches, reduce time to remediation, and minimize the scope of attacks with vulnerability management, endpoint detection and response (EDR), automated remediation, advanced hunting, sandboxing, managed hunting services, and in-depth threat intelligence and analysis about the latest malware campaigns and nation state threats.
The below table offers a comparison of capabilities are offered in Plan 1 versus Plan 2.

Taking it for a spin
Let’s go through an example of how a security analyst can use the capabilities of Microsoft Defender for Endpoint P1 to discover and investigate a security event.
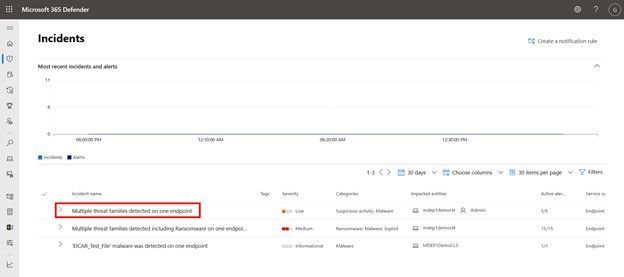
Security teams can access P1 capabilities through Microsoft 365 Defender at security.microsoft.com. Once logged in, you will land on the home page that offers a quick snapshot including a summary of active incidents, a view of your device health, and which devices may be at risk. Additional important links are located in the left-hand menu enabling teams to look at incidents and alerts, perform searches, see their device inventory, and access configuration management.

The incidents queue offers high level information about each incident including its severity, threat categories, impacted entities such as users and devices, and more. Let’s take a closer look at the incident named “Multiple threat families detected on one endpoint”.
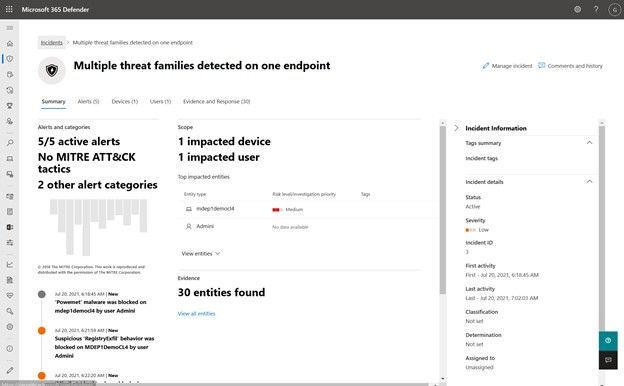
An incident is created by correlating related alerts and behaviors, giving security teams a holistic view of the potential threat so that they can quickly assess it and take action. On the incident page, the security team can further investigate with the additional details that are included such as all the alerts associated with the incident, which users and devices were affected, MITRE ATT&CK tactics used, and all the evidence that was collected.
On the alerts tab, let’s dive into the alert named “’Powemet' malware was blocked”. This alert was generated by our antimalware capabilities that offer behavior-based, heuristic, and real-time antivirus protection. Microsoft Defender for Endpoint offers one of the best antimalware capabilities in the industry with built in machine learning and behavioral monitoring, and consistently achieving top scores in independent AV tests.

In the Alert page, the security team can see rich and insightful information regarding the specific alert and the execution process. In this example we can see that Cmd.exe launched the attack that was detected as “Powemet”.
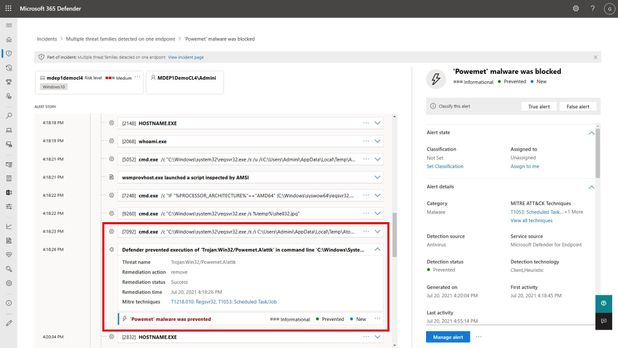
By analyzing the process execution tree and the flow of the attack, the security team can assess the threat and then take remediation actions directly from the Alert page. This can easily be done by clicking the ellipses next to the device at the top of the alert page. There, the security team has a range of actions available to them such as:
- Opening the device page for more detail
- Managing the device tags
- Performing an AV scan
- Collecting an investigation package
- Restricting app execution
- Isolating a device
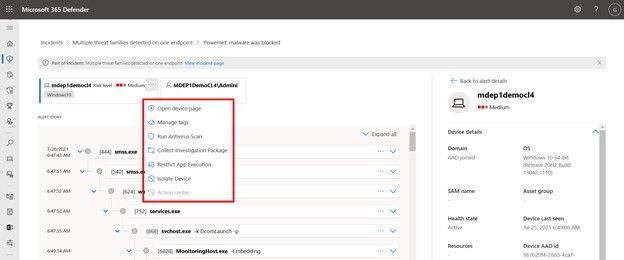
Depending on what is needed, the security analyst can take the appropriate action right in the console to continue their investigation and remediation steps.
Licensing
During this public preview, organizations can try out Microsoft Defender for Endpoint P1 for free. General availability is estimated to be later this year. Once generally available, Plan 1 will be offered in two ways:
- As a standalone SKU licensed per user. Eligible licensed users will be able to use Microsoft Defender for Endpoint Plan 1 on up to five concurrent devices.
- Included as part of Microsoft 365 E3/A3 with the same per user model and device entitlements as stated above.
For those customers that already have Microsoft 365 E3/A3, you will automatically get Microsoft Defender for Endpoint P1 capabilities when they become generally available. There will be a few steps you will have to take to enable this – we will share that information in detail closer to general availability.
Those organizations that own licenses that include Microsoft Defender for Endpoint P2 will not be eligible for P1. These licenses are already entitled to the full comprehensive solution that is P2.

How to get started
For detailed information on Microsoft Defender for Endpoint P1 capabilities and deployment guidelines please visit our documentation page.
Microsoft Defender for Endpoint P1 supports client endpoints running Windows 7, 8.1, 10, 11, macOS, Android, and iOS. To get started, organizations can sign up for the preview. After signing up, customers will be able to try P1 for free for 90 days. After the 90 days is up, we recommend that organizations work with their Microsoft account team or their cloud service provider (CSP) to purchase P1 licenses.
For detailed hardware and software requirements, please visit our documentation.
We’re excited to offer more options for organizations across the globe to be able to adopt our industry leading endpoint security capabilities. Customer feedback is critical to us and our development process. We are grateful to the many customers who have given us their input and look forward to hearing more from you. Please don’t hesitate to reach out with your thoughts either in the comments or by clicking on the “Give feedback” button in Microsoft 365 Defender.
