This post has been republished via RSS; it originally appeared at: New blog articles in Microsoft Tech Community.
There has been a long-standing divide between SCADA (OT) and Corporate (IT) cybersecurity disciplines. This divide was often driven by significant differences in technology, tooling, and expertise. Organizations are often required to operate multiple monitoring teams to cover these dynamics which inevitably increases risk for blind spots, inefficiencies, and complexity. Understanding the threat requires convergence of IT/OT monitoring in consolidated approaches. The Microsoft Sentinel: IT/OT Threat Monitoring with Defender for IoT Solution unites IT and OT, providing an unprecedented step toward protecting critical OT assets and securing your organization.

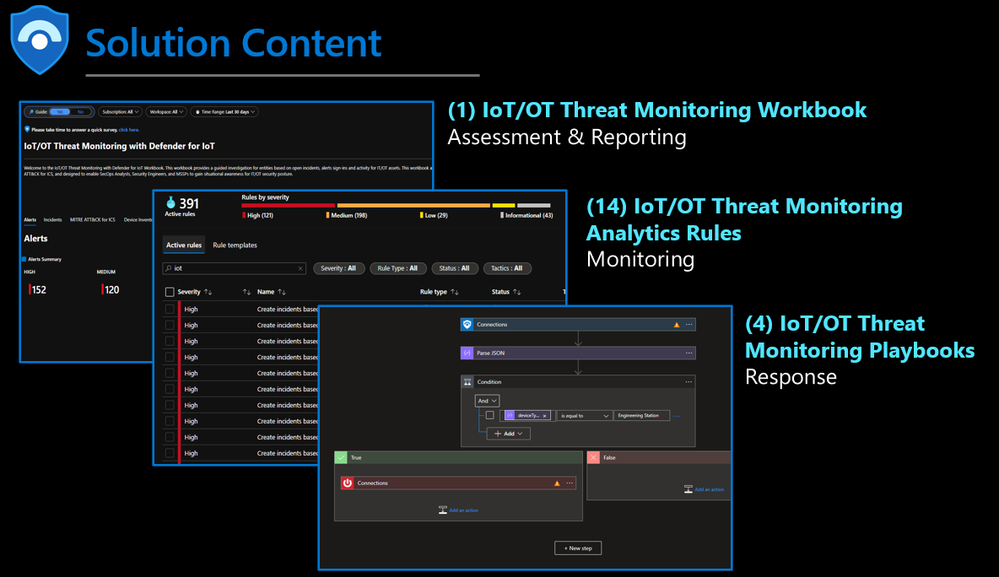
Content Use Cases
This solution provides the foundation for building a SOC for monitoring IoT/ OT and includes (1) workbook for visibility/reporting, (14) analytics rules for monitoring, and (4) playbooks for response. The workbook leverages Microsoft Sentinel telemetry to create visualization to understand, analyze, and respond to IoT/OT threats. Understanding alerts over time provides unprecedented insights into security posture and where teams need to focus to harden against threats. Deep links directly to Microsoft Defender for IoT alerts empower analysts to focus on remediating threats rather than pivoting between tools.
Benefits
- Detect, analyze, and respond to IoT/OT threats from a single pane of glass
- Assess security alert and incident response efficiency to improve SOC team capability
- Streamlined, consistent alignment between threat behavior and MITRE ATT&CK for ICS matrix
- Customizable reporting for subscription, workspace, and time filters
- Deep links integration for seamless pivots between Microsoft Sentinel and Microsoft Defender for IoT
- Device Inventory for identification, configuration, and baselining of OT
- Advanced analytics for detection of IoT/OT threats
- Playbook Automation for response to IoT/OT threats
Getting Started
This content is designed to provide the foundation for designing, building, and operating an IoT/OT monitoring team. Below are the steps to onboard required dependencies, review content, and provide feedback.
1) Onboard Microsoft Sentinel
2) Onboard Microsoft Defender for IoT
3) Connect Microsoft Defender for IoT to Microsoft Sentinel
4) Deploy the Microsoft Sentinel: IT/OT Threat Monitoring with Defender for IoT Solution
a) Microsoft Sentinel > Content Hub > Select IT/OT Threat Monitoring with Defender Solution > Install
b) In Government Regions, leverage the Deploy to Azure Gov button from the GitHub ReadMe for deployments.
5) Review the IT/OT Threat Monitoring with Defender for IoT Workbook
a) Microsoft Sentinel > Workbooks > Select IT/OT Threat Monitoring with Defender for IoT
6) Review the IT/OT Threat Monitoring with Defender for IoT Analytics Rules
a) Microsoft Sentinel > Analytics > Search “IoT”
7) Review the IT/OT Threat Monitoring with Defender for IoT Playbooks
a) Microsoft Sentinel > Automation > Playbooks > Search “IoT”
8) Review the content and provide feedback through the survey
Frequently Asked Questions
- Are custom views and reports supported?
- Yes, via subscription, workspace, time, parameters.
- Are additional products required?
- There are not additional product requirements beyond Microsoft Sentinel and Microsoft Defender for IoT.
- Is this available in government regions?
- Yes, this is deployable in all environments.
- What rights are required to use this content?
- Security Contributor can create and edit workbooks, analytics rules, and other Microsoft Sentinel resources. Security Reader can view data, incidents, workbooks, and other Microsoft Sentinel resources.
Learn More About Defending IoT/OT with Microsoft Security
- Enabling IoT/OT Threat Monitoring in Your SOC with Microsoft Sentinel
- Defender for IoT product summary
- Cloud-delivered IoT/OT threat intelligence
- 5 steps to enable your corporate SOC to rapidly detect and respond to IoT/OT threats